Microsoft just launched the preview for the “Text message” authentication method, for Azure AD users. Let’s try it out.
First, enable the new feature under authentication methods:


After the feature has been enabled, the “Authentication methods” tab on the user page, should now have a new feature:
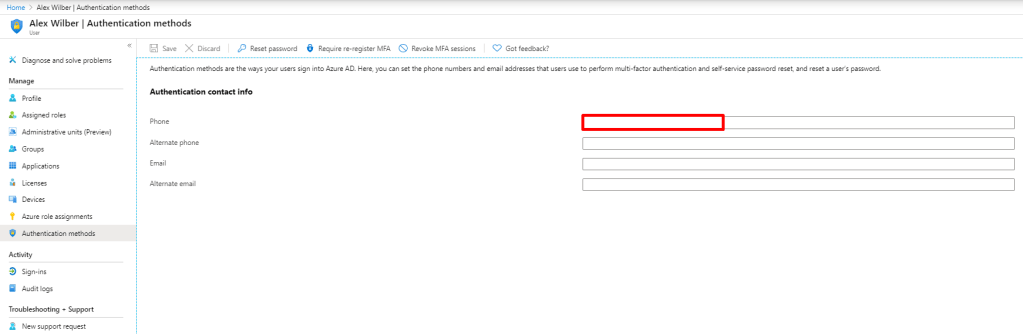

After filling in a phone number and saving, a checkbox appears with “SMS sign-in ready”. Now, let’s try “portal.office.com”:

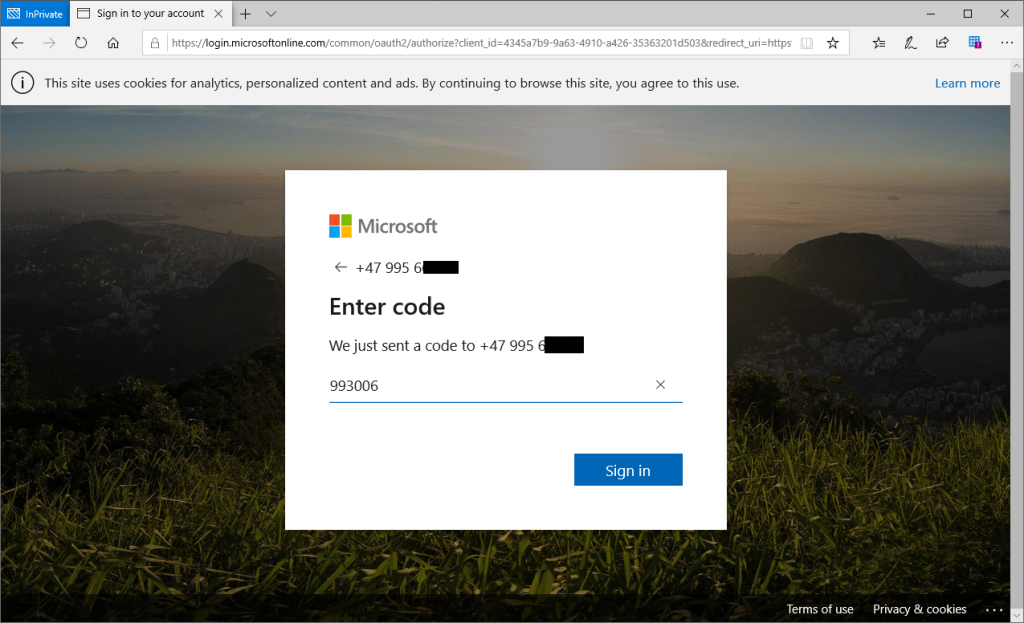
So hey, this works:

But – I authenticated at the common endpoint. Does this mean that the authentication phone must be unique across all tenants? Let’s test this out using another test tenant.

Phone number now being authentication phone on two different accounts in two different tenants. What will happen now?
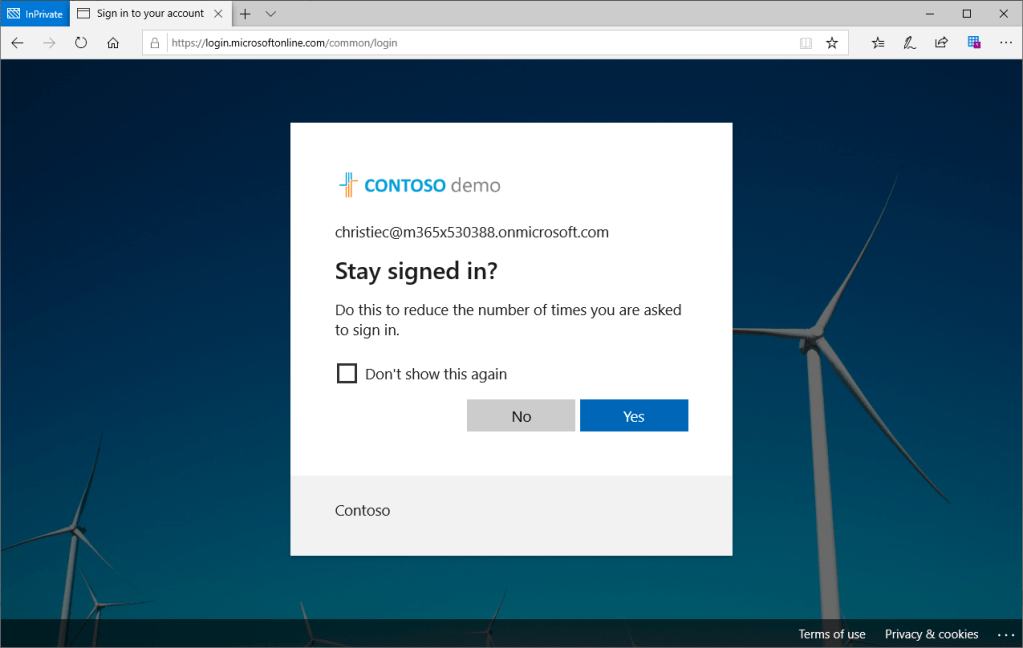
Apparently I became this user, which is the second user i added the phone number to? So apparently, if someone in another tenant just types your phone number on one of their users by mistake, you are now signing in as them? This opens for a whole new kind of DoS attack…
EDIT: This was an experience that only happened during the first rollout weekend for the feature, and you are now presented with an account picker (see bottom of post)
A simple modify value back and forth on AlexW make the auth happen to that user instead:

Trying a tenant specific endpoint (portal.azure.com/M365x530388.onmicrosoft.com) now:
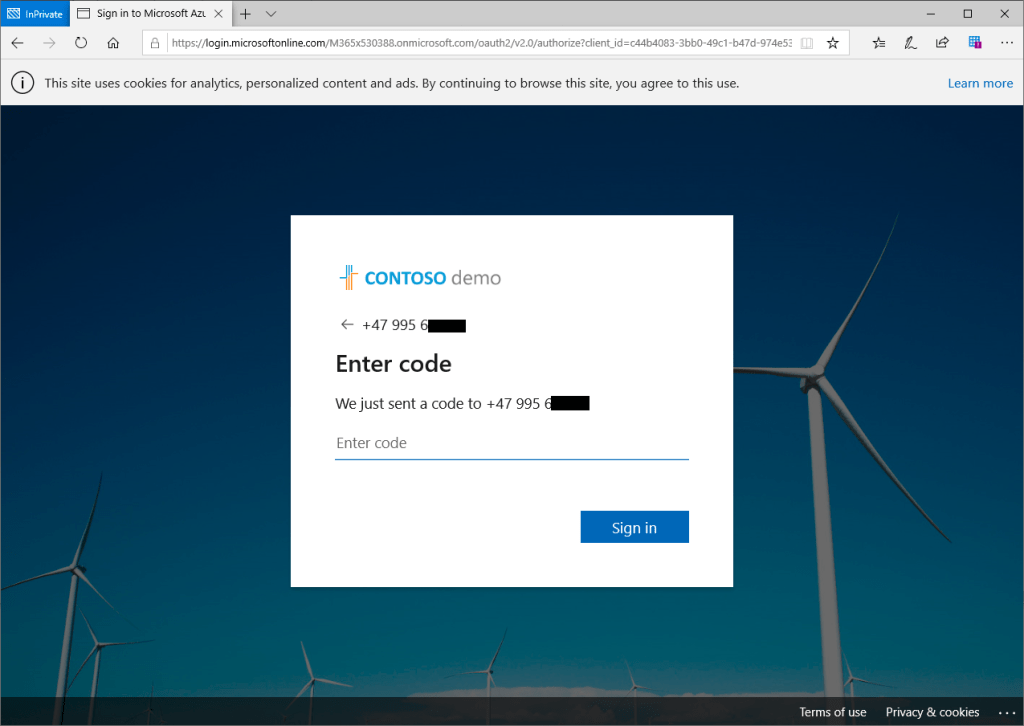

Here i become the other user again. So apparently, the common endpoint routes the user to the last modified authentication phone.. Not really optimal to be honest.
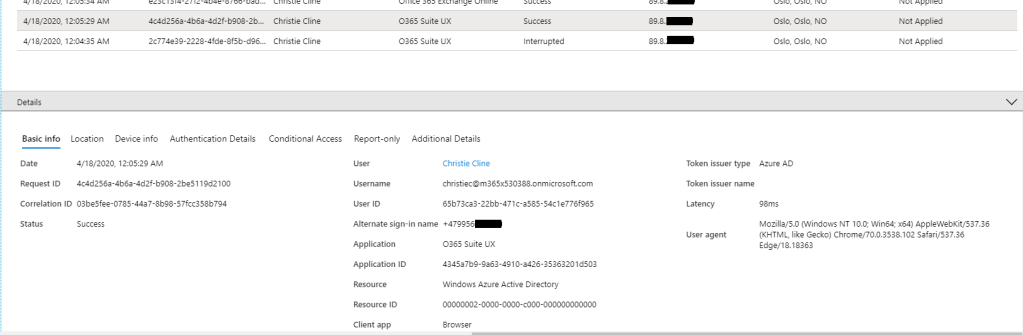
The sign in log for the user contain an entry where the “alternate sign-in name” is set to the phone number of the user:
So yeah, it works, but i believe the whole common endpoint issue should be addressed somehow 🙂
EDIT:
The account picker experience has been updated with the following experience:

One thought on “Trying out the new phone sign in feature for Azure AD”