With Azure AD External Identities, Microsoft is bringing some of the Azure AD B2C features to “regular” Azure AD, and it is now generally available (GA). With these features, you can add public self service sign up-baed authentication flows to your services, using your existing Azure AD.
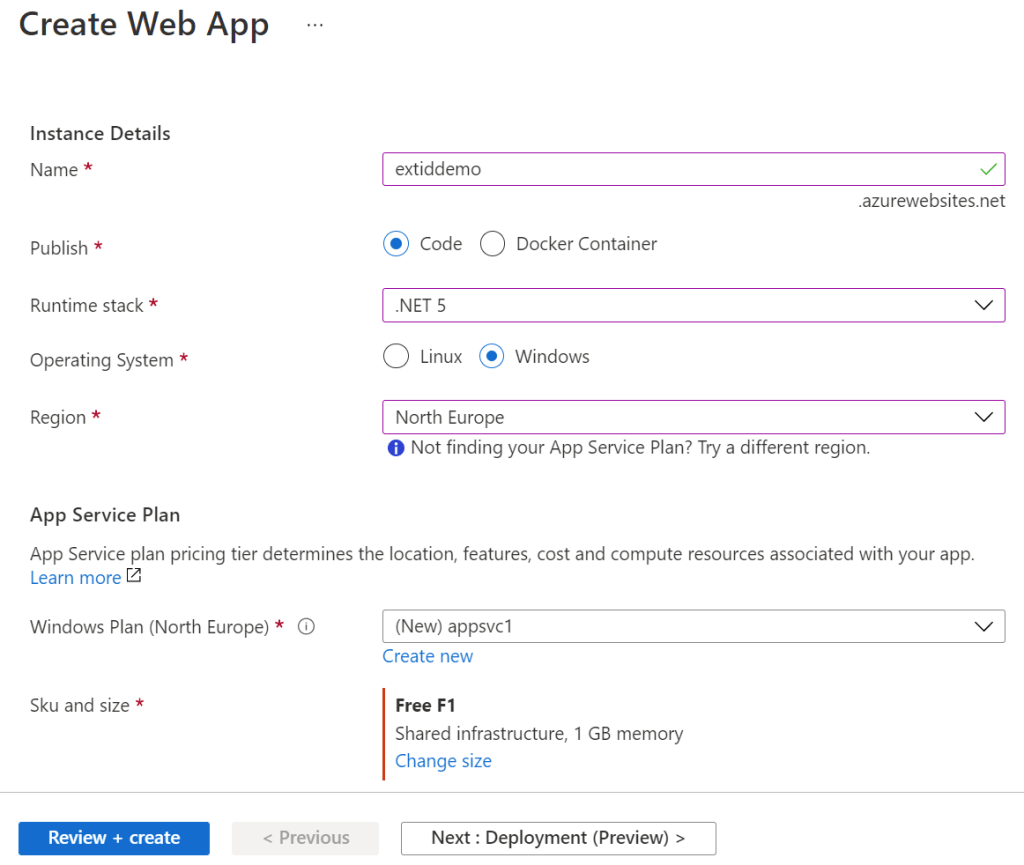
Let’s start by creating a simple Azure web app using the built-in Azure Active Directory authentication in the Azure app service.
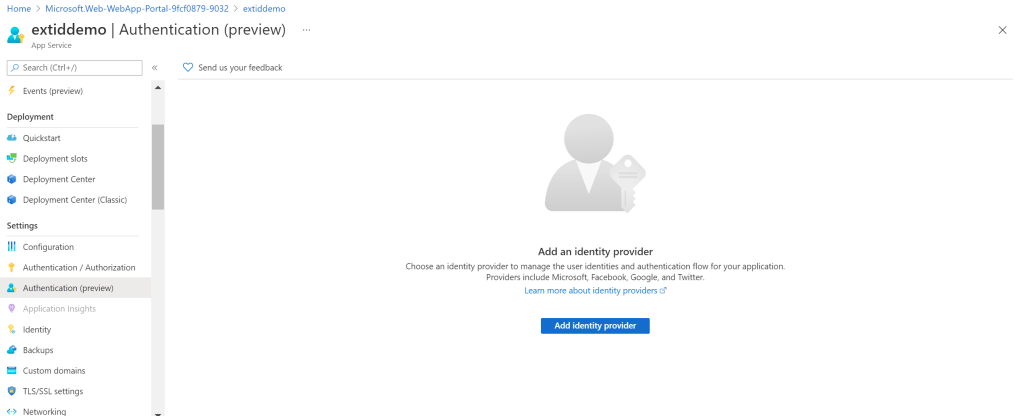
After the web app has been created, we establish authentication by choosing Authentication (Preview) in the left pane, or you can use the non-preview option:
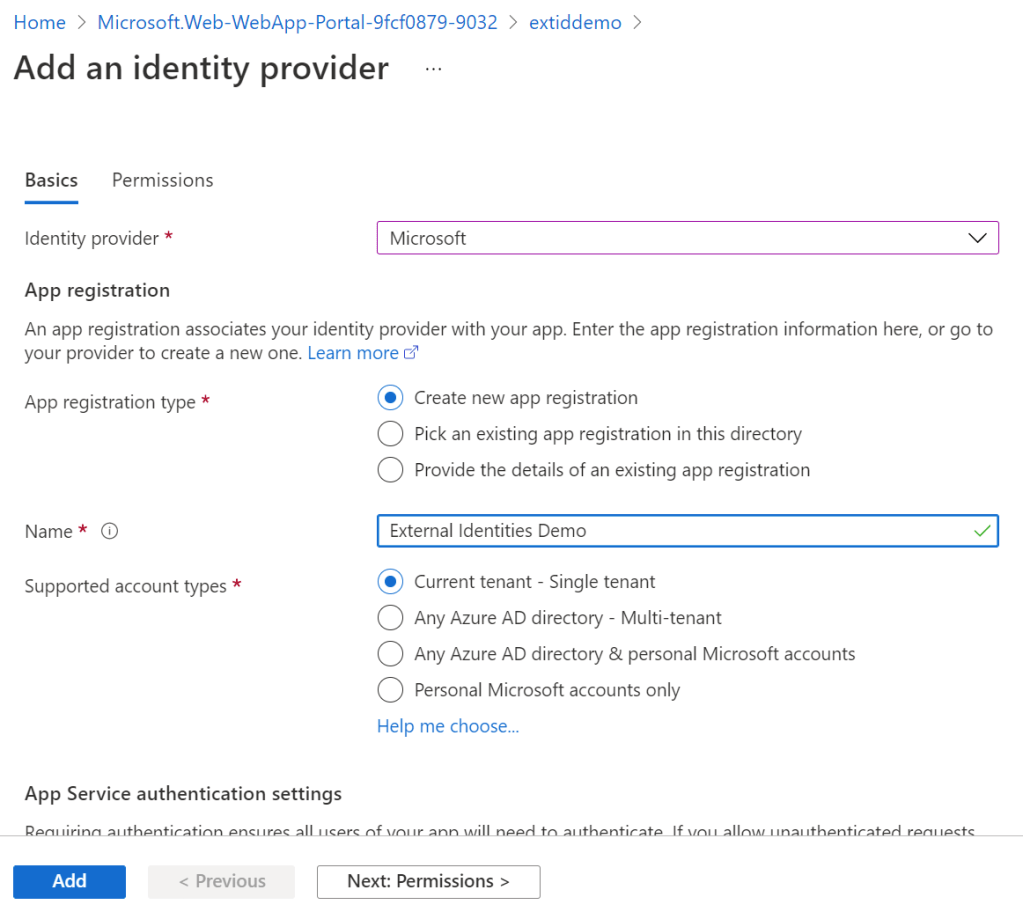
Give the application a name, and choose single tenant authentication. Why?
Well, we are using external identities, and with external identities, authentication happens in your tenant using a combination of B2B and B2C flow. If you, as many would have thought, chose multi-tenant application here, the authentication would happen towards the common endpoint where no B2C flow is possible and where any tenant can simply consent to using your app without going through the user flow configuration in external identities.
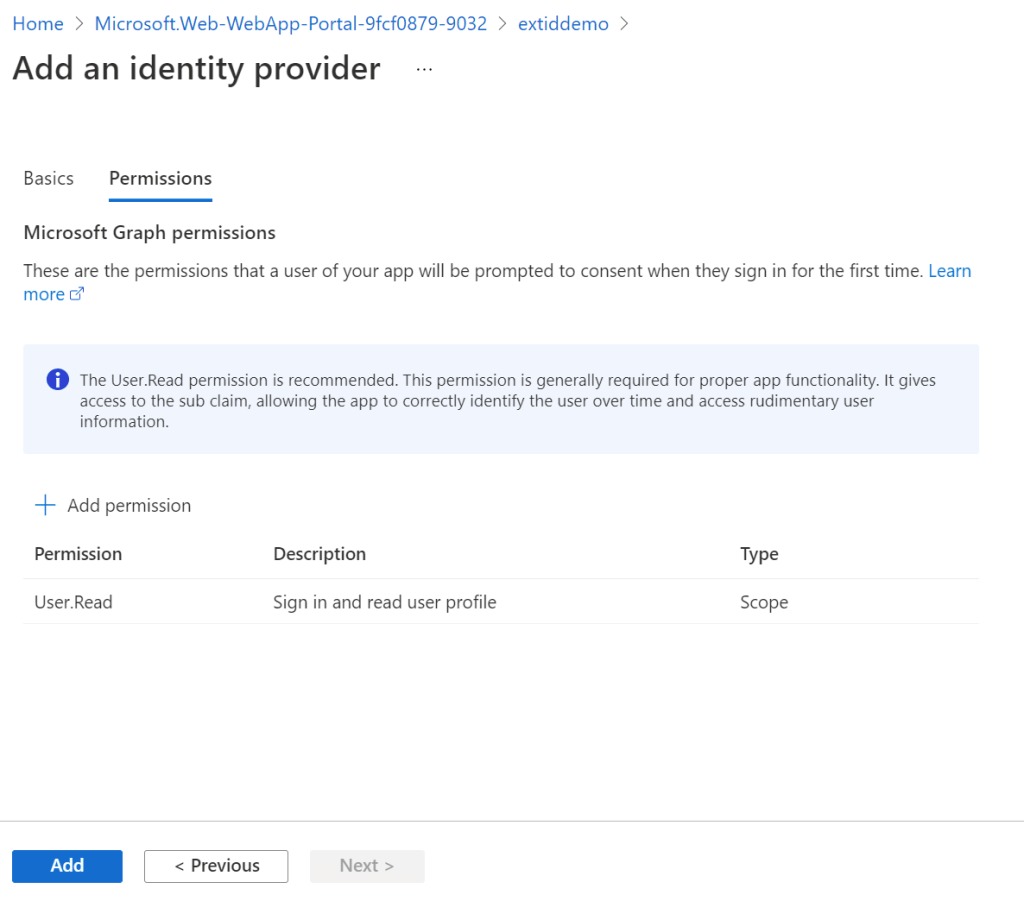
Leave permissions as default
After enabling authentication, we can now go to our web app url https://extiddemo.azurewebsites.net and experience that it now requires authentication, and that the first time someone signs in they must consent to the app. This happens because no one has consented to the application, in the app registration gui yet.
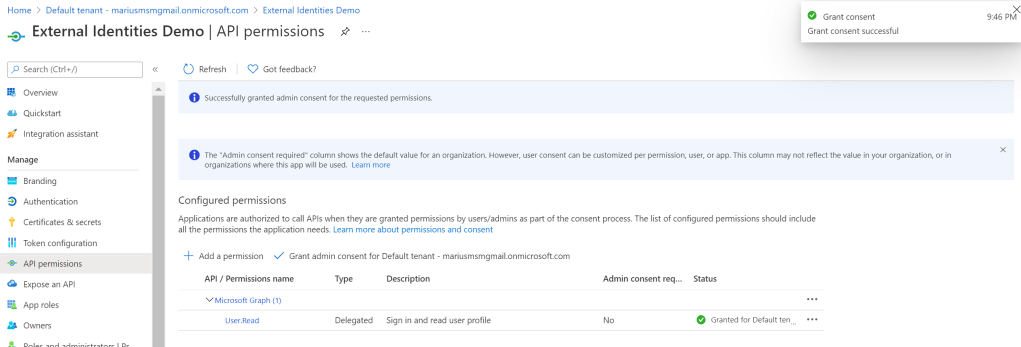
You can either choose to delegate on behalf of your organization on this screen:
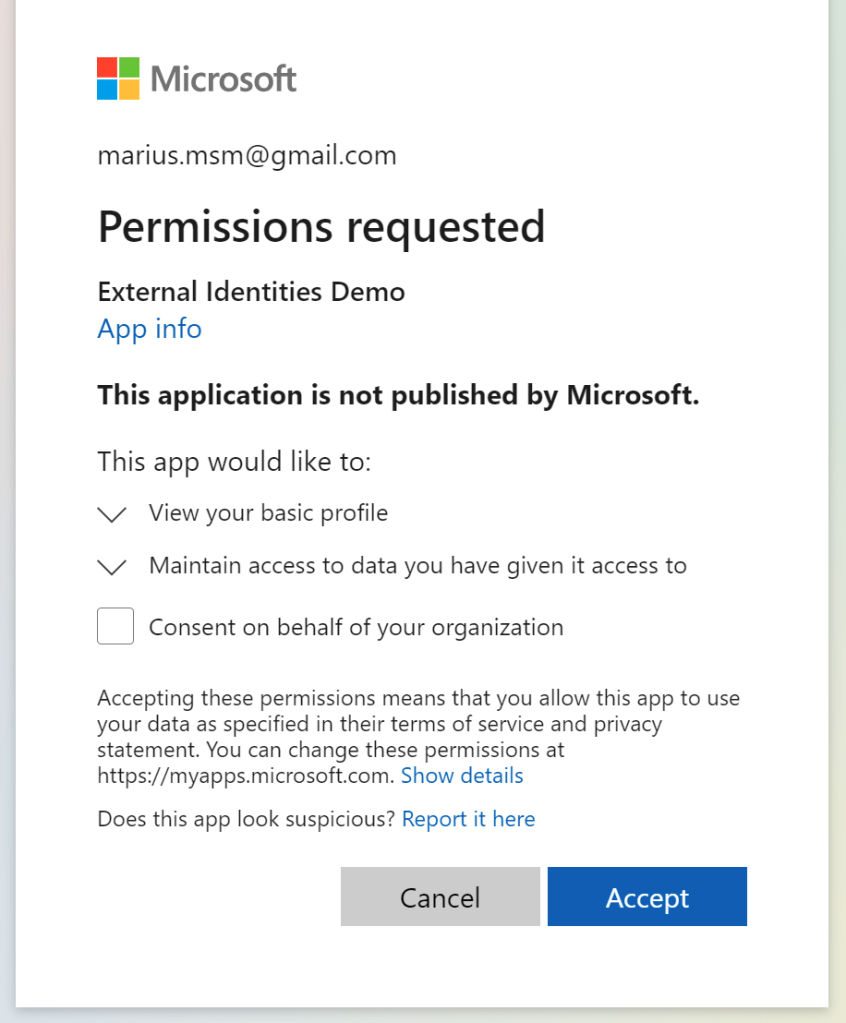
Or on this screen:
You might experience MFA etc. when signing in, depending on the conditional access policies in your tenant.
At this point, the users allowed to sign into the application are:
- Local users in your tenant
- B2B guests in your tenant
This is based on the following setting on the Enterprise App, plus the fact that it is a single tenant application:
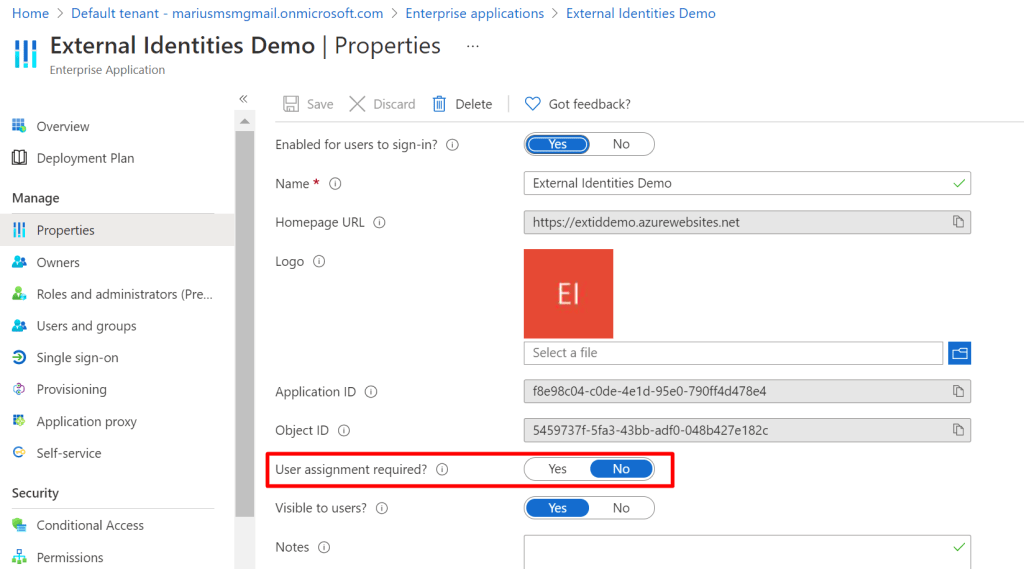
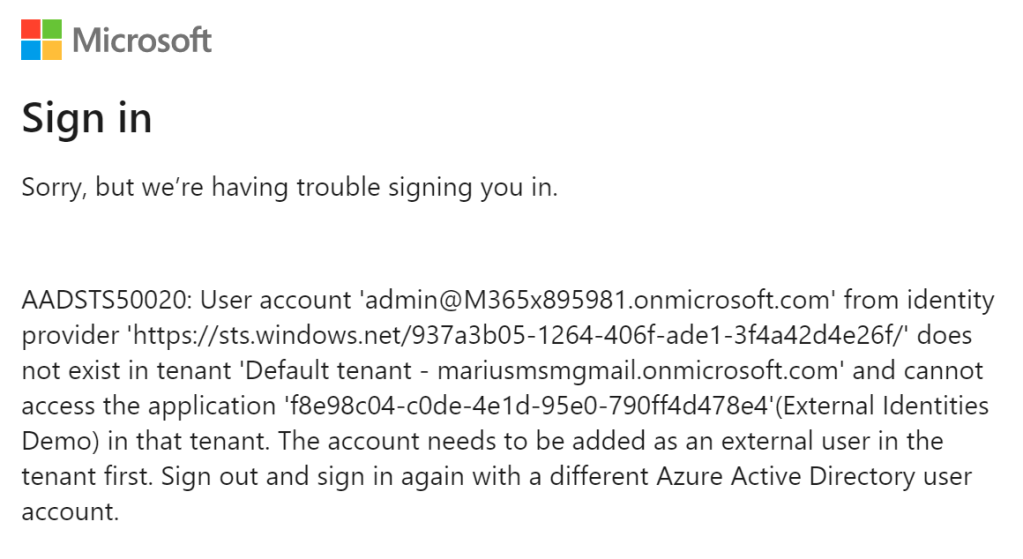
Trying to sign in with a random external users yields the following error:
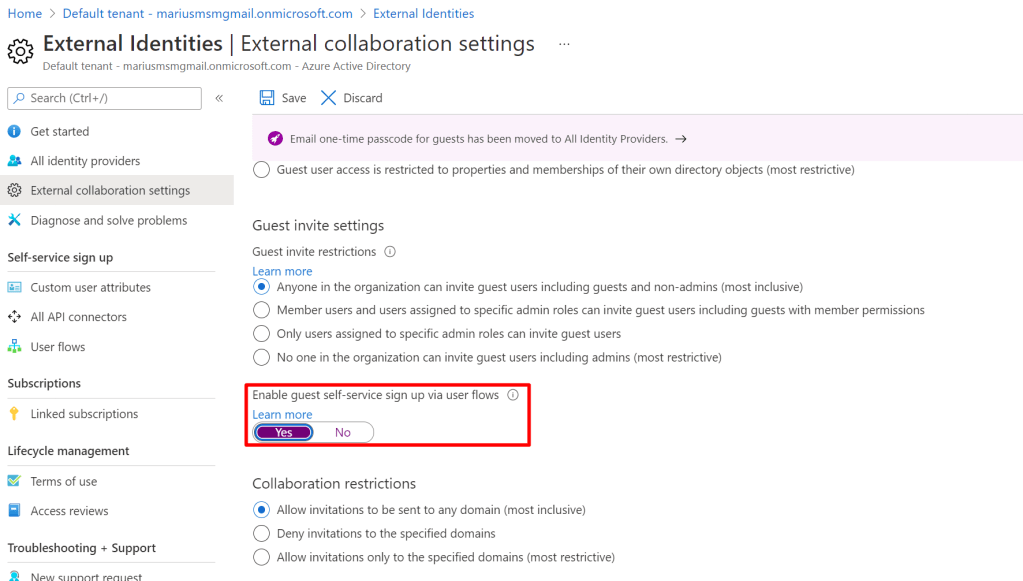
We are now ready to enable self service sign-up. First we must enable the User Flows feature:
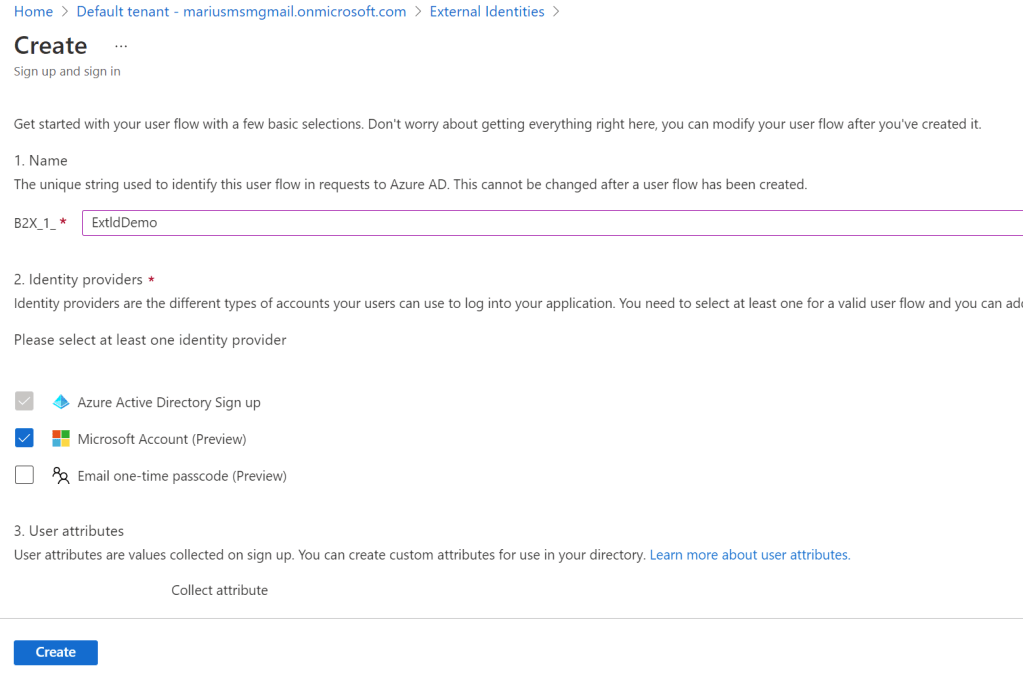
And then we can create a new User Flow:
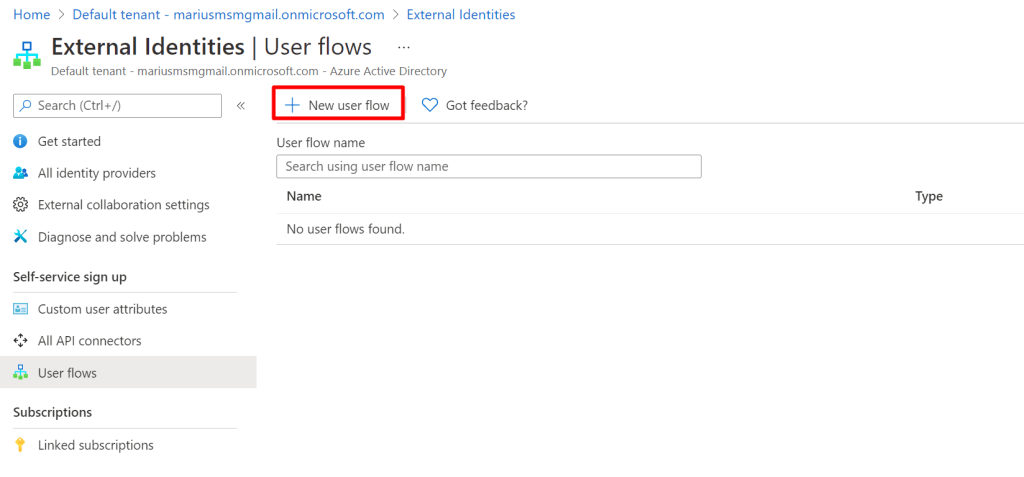
Name the user flow, choose Microsoft Account and Azure Active Directory sign-up – and click create. Enabling email one-time passcode disables Azure AD sign-up, just so you are aware.
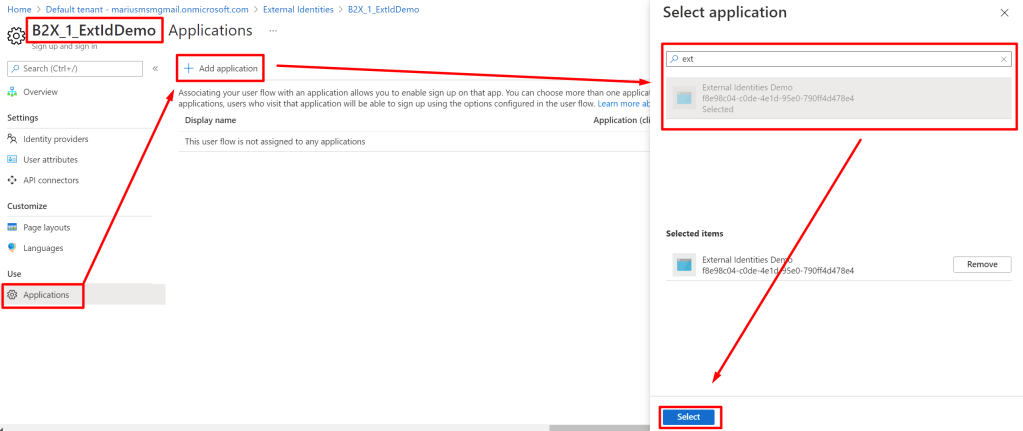
After creating the user flow, assign the application to it as follows:
After this, we’ll receive a new user experience when signing into the app:
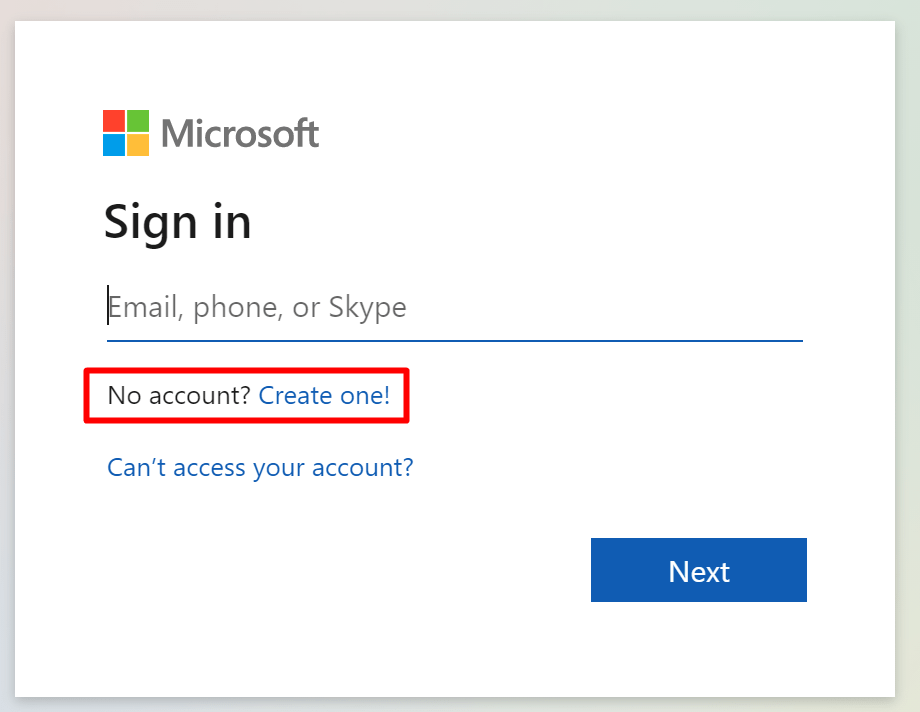
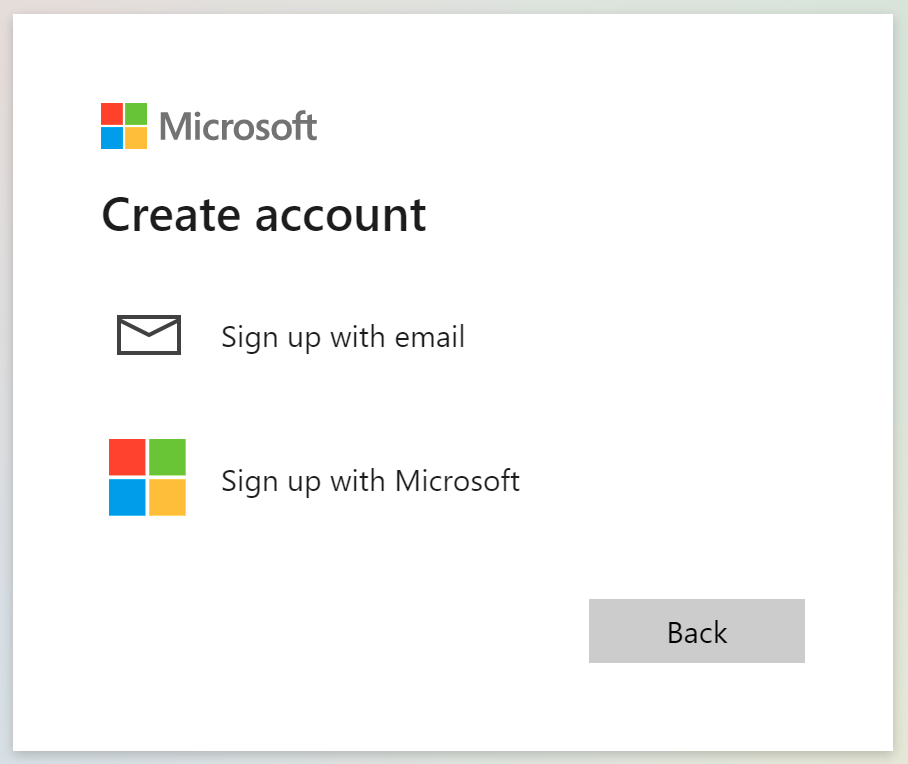
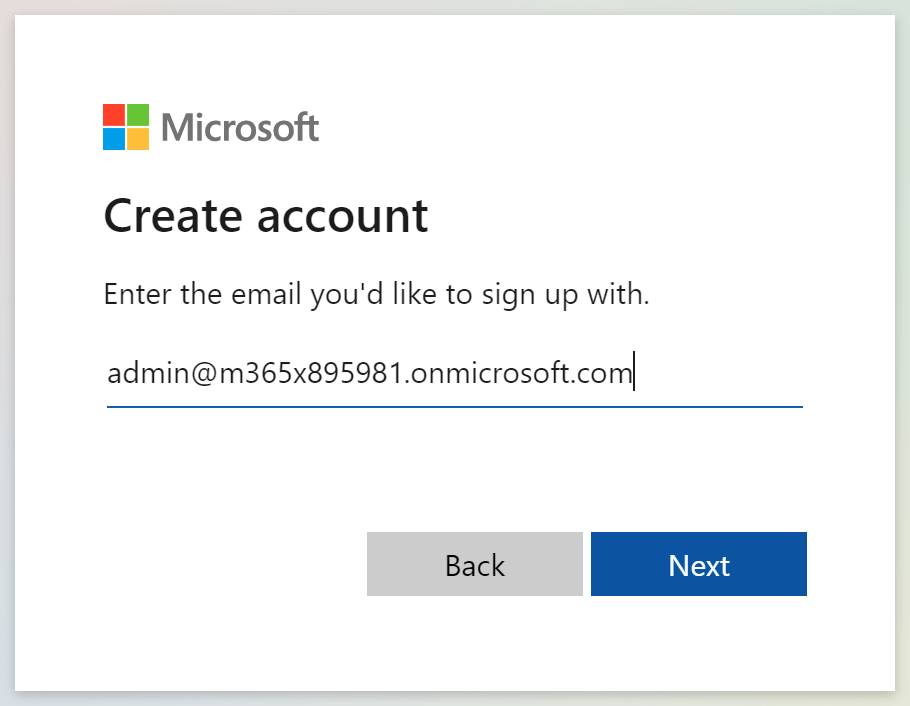
When signing up with an Azure AD account, we need to choose “Sign up with email”. We can now type our email address:
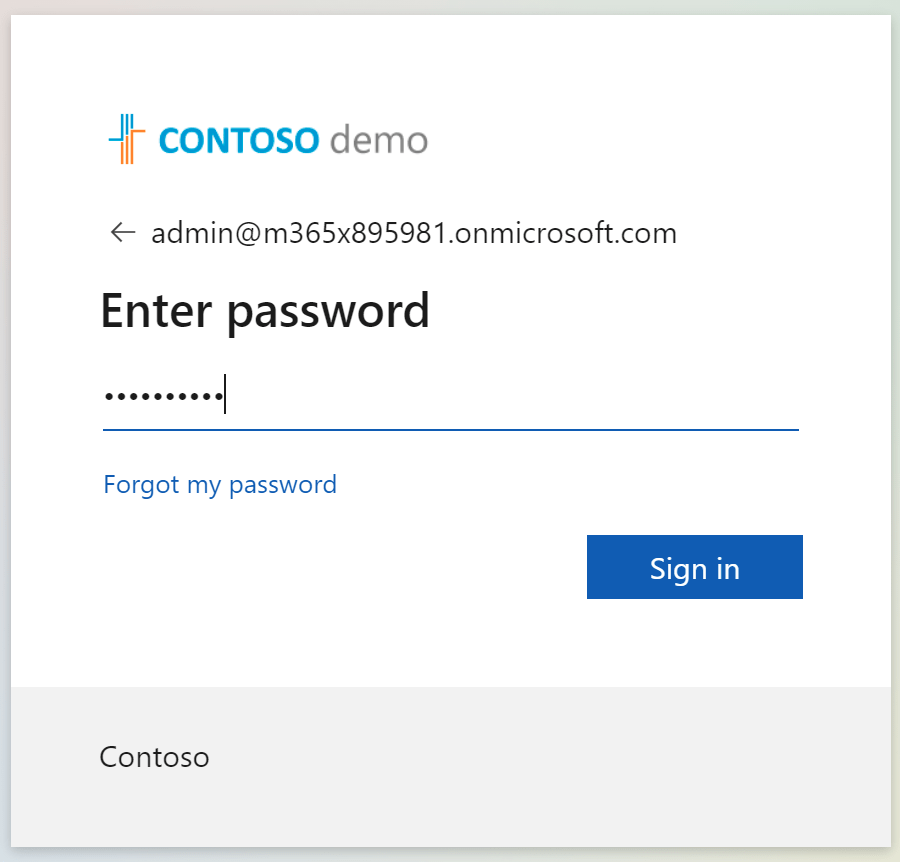
Which will send you to signin into your own tenant:
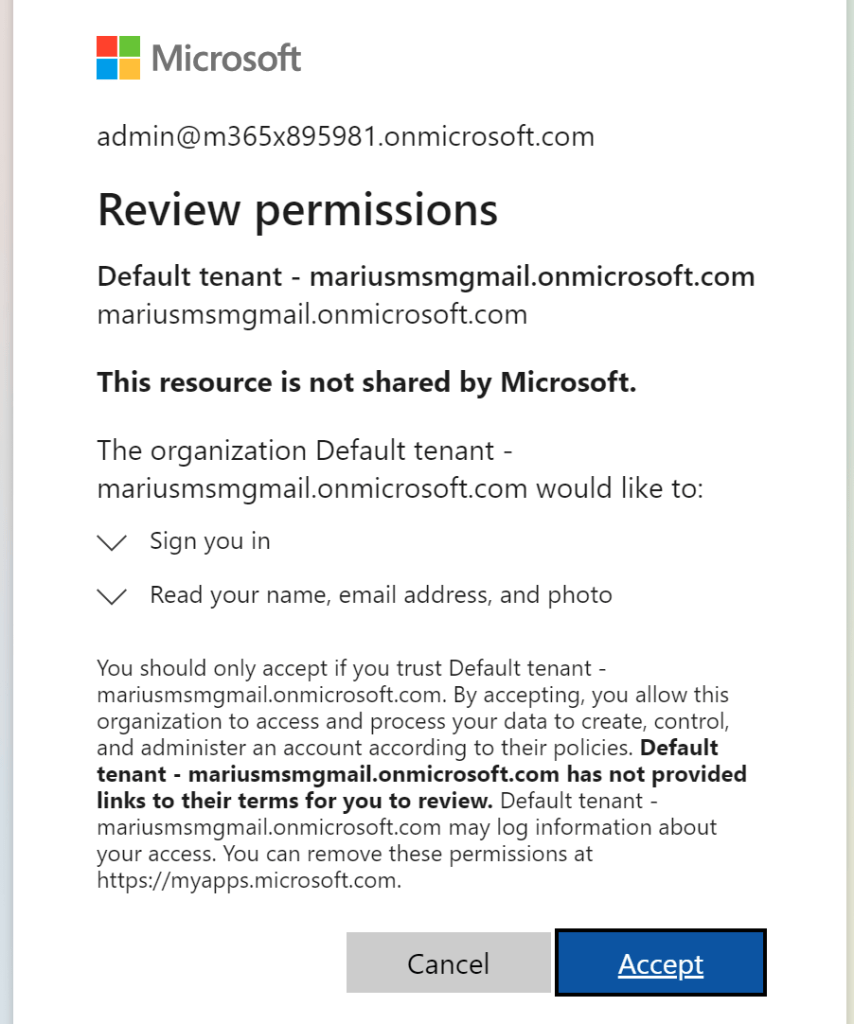
And after that, you’ll receive the regular “B2B consent screen”. Here you should add privacy contact, in order for this page to not display the “has not provided links to their terms” message:
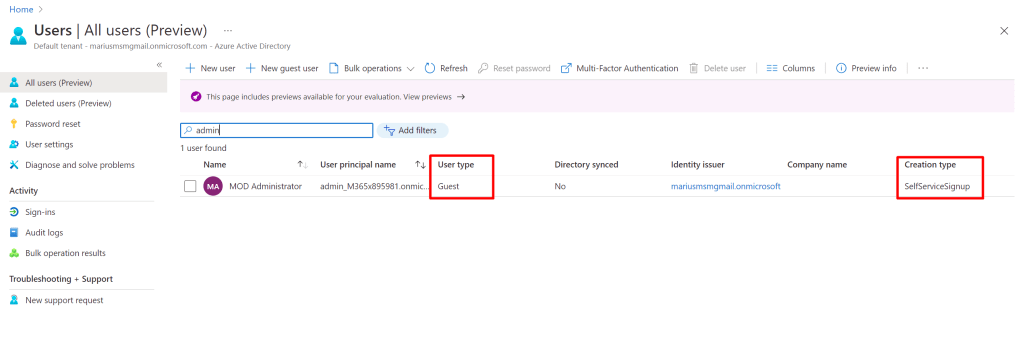
In Azure AD, we can now find a new B2B guest account created through self service sign up:
What is really awesome now, is that regular Azure AD features, such as conditional access and identity protection still works just fine, protecting these external acocunts. This means that you can:
- Block external users with high risk (caused by things like leaked credentials)
- Require MFA, and soon even requring MFA conditionally based on opeartions in apps (feature soon to come in preview)
- Require signing of terms of use
Additionally, you can do things like:
- Trigger a Logic App or Azure Function (or API call) on the sign-in and sign-up event
So yeah, please go ahead and use this for your applications! 🙂
Thanks great blogg