So, you are attacking Azure? Or you want to test out something in the context of a user assigned identity? In this blogpost I’ll show you how create an access token for any Azure API, Microsoft Graph API, etc. for a user assigned identity.
A user assigned identity is a kind of service principal where Microsoft is responsible for handling the certificate or secret (essentially all parts on the app registration level), while you simply call certain endpoints from your code, and those endpoints will issue an access token to you.
There are many Azure services that support user assigned identities, such as Azure Functions, LogicApps and Azure Virtual Machines. The main difference between user assigned identities and a system assigned identity, is that a system assigned identity is tied to a single Azure resource, while a user assigned identity is a resource in its own and can be assigned to multiple Azure resources. This means that 10 different LogicApps can be assigned the same user assigned identity.
Using the fact that we can assigned a user assigned identity to multiple Azure resources, there a very simple ways of creating access tokens for user assigned identities: Create an Azure Function -> Assigned user assigned identity -> Run Azure Function.
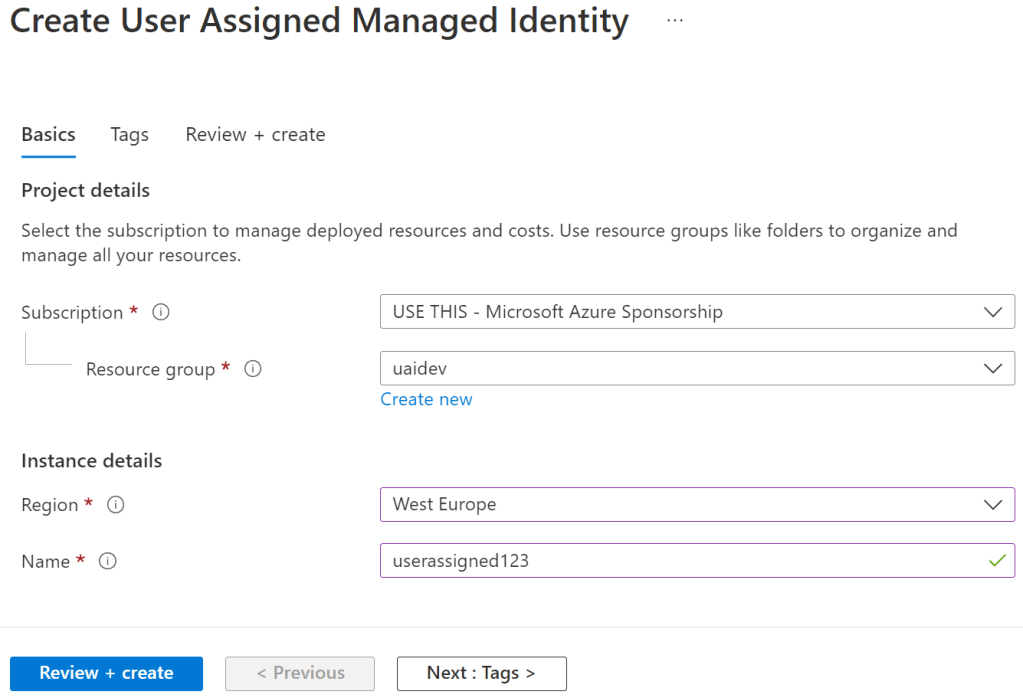
Let’s first create a user assigned identity:

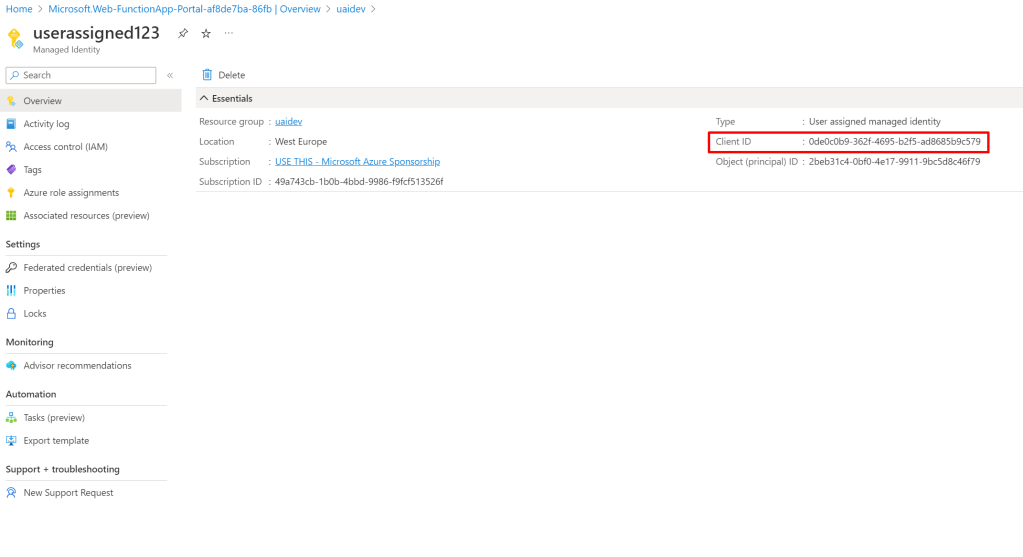
We now have a user assigned identity:

Click on it and copy the Client ID, as we’ll use it later:
We will now create a free Azure Function:

Make sure your runtime stack i PowerShell Core (Works on any stack, but this example is for PowerShell).

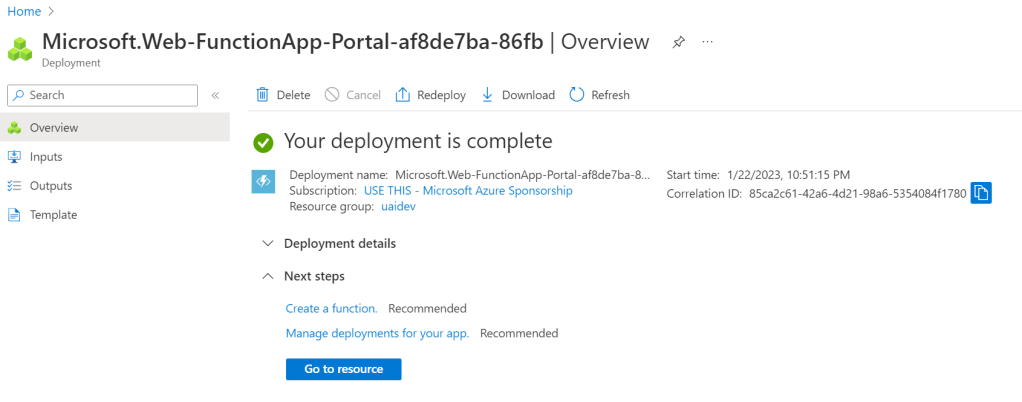
Click Review + Create and Create.
Now that the function app has been created, click Go to resource:
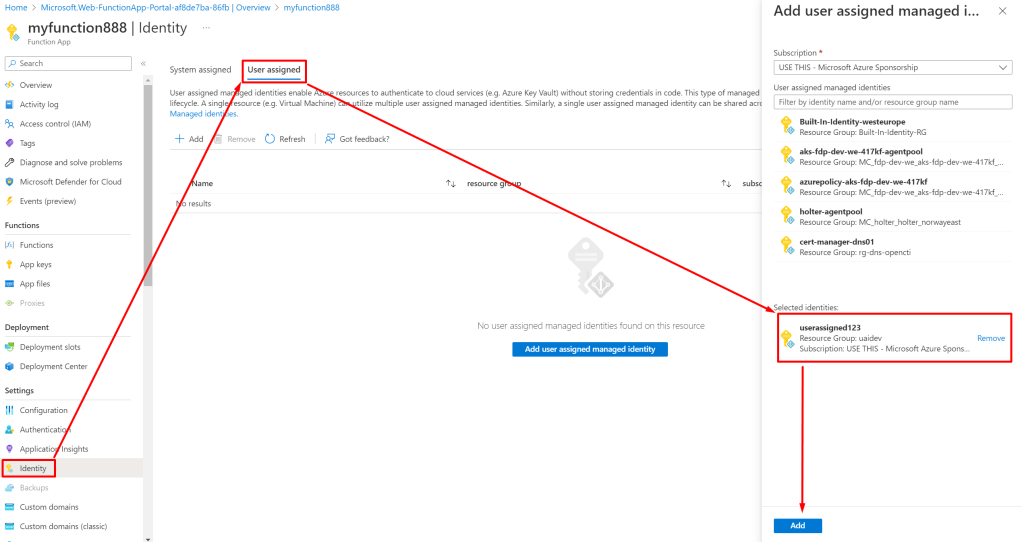
Click on Identity, choose User assigned, find your user assigned identity and click Add.
Next, create a function by going to Functions, clicking + Create, choosing HTTP trigger, give the function a name and click Create.

Now you will be sent to the edit page of the function, click Code + Test and paste the below code, replacing the guid 0de0c0b9-362f-4695-b2f5-ad8685b9c579 with the clientid of your own user assigned identity:
using namespace System.Net
# Input bindings are passed in via param block.
param($Request, $TriggerMetadata)
$resource = "https://graph.microsoft.com"
if($Request.Query.resource) {
$resource = $Request.Query.resource
}
$uri = "$($env:MSI_ENDPOINT)?clientid=0de0c0b9-362f-4695-b2f5-ad8685b9c579&api-version=2017-09-01&resource=$resource"
Write-Verbose $uri
Write-Output "uri: $uri"
$authenticationResult = Invoke-RestMethod -Method Get -Headers @{'Secret' = $env:MSI_SECRET} -Uri $uri
# Associate values to output bindings by calling 'Push-OutputBinding'.
Push-OutputBinding -Name Response -Value ([HttpResponseContext]@{
StatusCode = [HttpStatusCode]::OK
ContentType='application/json'
Body = @{
access_token = $authenticationResult.access_token
} | ConvertTo-Json
})

Try Test/Run, and you have your access token!

By default, the access token is create for the Microsoft Graph. If you need an access token to other APIs, simply send the resource parameter:

That’s it now, go hack your user assigned identities!