Dropping a quick Terraform module that automatically rotates the password of an Azure AD application, outputting the value into an Azure DevOps variable group. This can be super handy when maintaining a tenant by code, allowing developers to “order” app secrets.
Continue reading “Terraform module for automatically maintaining Azure DevOps variable group with app secret”Category: Uncategorized
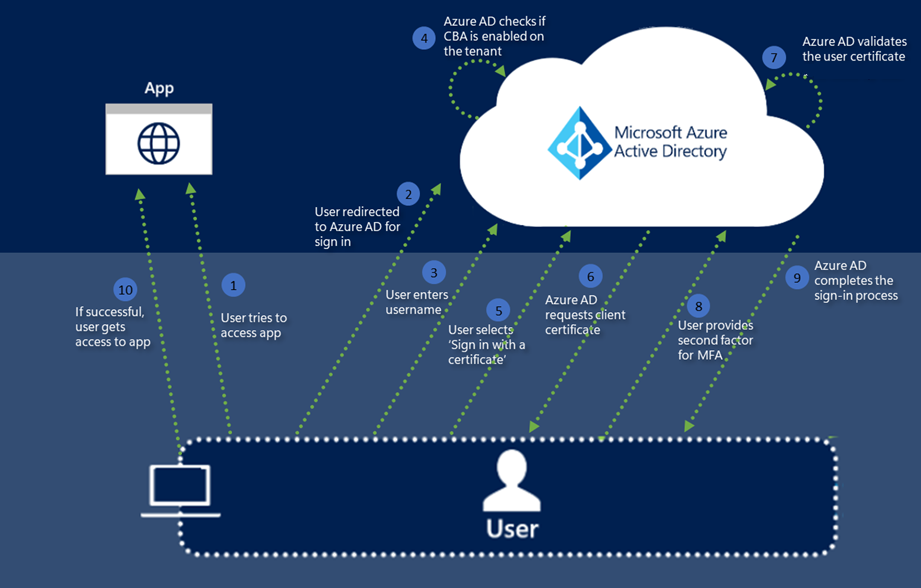
Digging into Azure AD Certificate-Based Authentication
Azure AD Certificate-Based Authentication is now in public preview, with a surprisingly good documentation. Usually I have to guess how 50% of a feature actually works, but this time they have gone all-in with technical details of just about everything. What is a blogger to do? Well, let’s configure it and see if we can sneak a peek behind the scenes 🙂
Finding Azure AD domain from tenant id
Ever had an Azure AD tenant id, and wondered which tenant this is? While checking the APIs behind the new Azure AD cross-tenant access settings, I found a new API that can help you with this!
Continue reading “Finding Azure AD domain from tenant id”Azure IP Ranges Terraform Module
There is no reason to have your services available from the entire internet, if you don’t need to, but often it can be difficult to maintain allow lists for public cloud IP addresses. Not anymore. I have built a Terraform module that updates itself from the Microsoft provided JSON of IP addresses.
Checking out Azure AD cross tenant access policies
So, as one does, I was checking out the different Microsoft Graph AppRoles, which are the application scopes available. And then I found this:

Now, I now cross tenant access is something Microsoft has been working on for a while, and I have seen some preview stuff presented, but I have no access to any preview at all at this point. However, let’s see what we can find!
Disclaimer: Do not use this in production, as it is only a private preview feature I discovered.
Continue reading “Checking out Azure AD cross tenant access policies”Another deep dive into Azure AD Workload Identity Federation using GitHub actions
I just had a previous blogpost about Workload Identity Federation, where I went into the details of how authentication works. This time, I want to use GitHub actions, which is the currently supported method. There are some limitations to the documentation today, but hopefully we will be able to do things like accessing KeyVaults and other services, not only using Azure CLI.

A deep dive into Azure AD Workload identity federation
Workload Identity Federation is a rather new concept in Azure AD, where service principals do not have keys in a directory, but in stead is federated to an external OpenID Connect (OIDC) provider, such as Okta, Ping, Github, GCP, AWS and – well – Azure AD.
A part of an earlier blogpost used a JWT in a client credential grant, signed by a KeyVault based certificate, to authenticate as an application. This time, this JWT will not be signed by a certificate, but instead by an OIDC provider.
Continue reading “A deep dive into Azure AD Workload identity federation”Quick look at managing Azure AD Custom Security Attributes using Graph
Brand new feature out in public preview, and here is how to manage it using Graph. The documentation is already quite decent.
Continue reading “Quick look at managing Azure AD Custom Security Attributes using Graph”Script to create named locations for Azure regions
Just built a quick little script that creates named locations for conditional access based on the IP addresses provided and updated by Microsoft, through a json file.
By using this script to manage named locations, you can, through the workload identities conditional access policies currently in preview, limit where your service principals can be used from. You can say things like “These service principals can only be used from Azure region West Europe”.
Testing out conditional access for workload identities
At Ignite, Microsoft made the conditional access for workload identities feature available in public preview. Currently, this feature is quite limited in scope, but let’s see what it can do.
Continue reading “Testing out conditional access for workload identities”