I have now configured many SharePoint Management Agents, and initially I had severe problems finding out which attributes to populate with what. Here is the lessons I learned during this investigation.
Application ID
During configuration of the Management Agent, you are requested to input Application ID. I have never used it, and i guess it is used when you have multiple User Profile Service Applications.
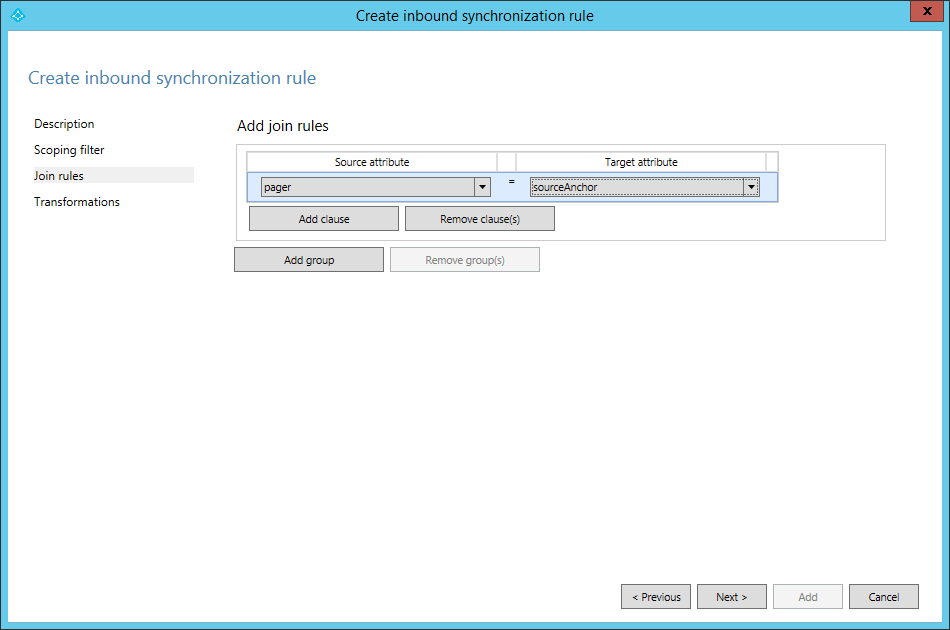
Anchor
Do not bother with anchors. Instead just provision a connector space object and let it get the default anchor. You will never see the anchor anywhere except in FIM and internally in the SharePoint databases.
Manager attribute populating bug
There is a bug in SharePoint, where the manager attribute won’t be populated in the User Profile Service, even though you are flowing it with FIM. The reason is that the timer job “User Profile Service Application – User Profile ActiveDirectory Import Job” is not created if you configure “Enable External Identity Manager” directly. Instead, you have to first choose “Use SharePoint Active Directory Import” on the “Configure Synchronization Settings”, and let this job be created (takes 15 minutes), then switch to “Enable External Identity Manager”.
Parallellism
It is not supported to run multiple SharePoint MAs simultaneously. Not sure why, but a little bit of code snooping shows this is true.
Pictures
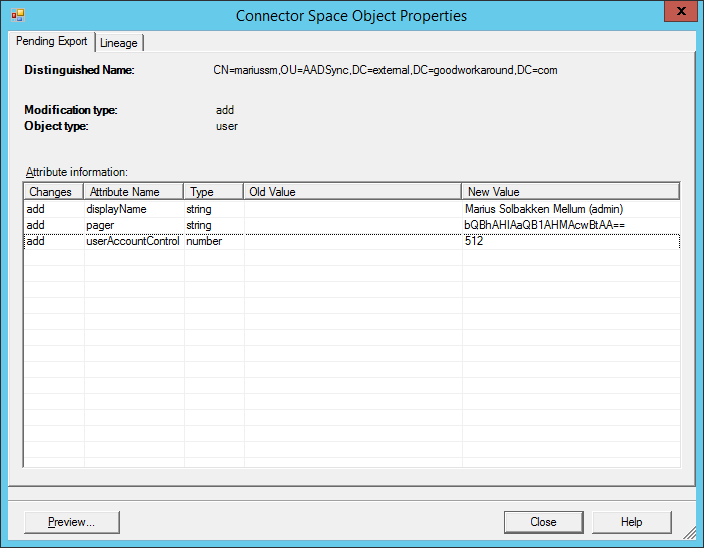
Pictures can be a bit difficult, especially when trying with limited permissions. First of all, if you use fiddler the attribute is actually called “PictureURL”. Also, technically it seems as though what actually happens when you use this connector and export a picture, you transfer the binary data (as base64 ofc) out in “PictureURL / Picture” and the API you talk to uploads these data as an original to your mysite, at the location “http://mysitehost.goodworkaround.com/User photos”. And then it stores the url of the picture in the User Profile Service.
First of all, the MySite host MUST BE IN THE SAME FARM. It is not possible to have pictures uploaded to a separate SharePoint farm. Second, there is a requirement for permissions on the mysitehost. You can grant these permissions with the following cmdlet:
$w = Get-SPWebApplication -Identity http://mysitehost.goodworkaround.com
$w.GrantAccessToProcessIdentity("gwrnd\managementAgentAccount")
If you do not give this permissions, FIM will not get any error message from SharePoint saying “sorry, we could not store this picture”. It will simply be “ok” even though the picture was not saved.
Also, as you can see in this TechNet article you need to run a cmdlet to actually generate the thumbnail photos.
ADFS authentication
To configure ADFS authentication the following attributes needs to be flowed from FIM to SharePoint:
| SharePoint attribute | Value |
| SPS-ClaimProviderID | Name of the trusted identity provider in SP (case sensitive): “SAML Users” |
| SPS-ClaimProviderType | Constant: “Trusted” |
| SPS-ClaimID | Unique identifier – mail, userPrincipalname, employeeID etc. Must be what comes in the nameidentifier claim from ADFS |
| SID | Do not flow anything |
| ProfileIdentifier | someprefix:unique – where “unique” is the same as SPS-ClaimID (not required, but make it unique) |
| UserName | Do not flow anything |
| AccountName | Do not flow anything |
Example user
| SharePoint attribute | Value |
| SPS-ClaimProviderID | SAML Users |
| SPS-ClaimProviderType | Trusted |
| SPS-ClaimID | marius@goodworkaround.com |
| SID | no flow |
| ProfileIdentifier | gwrnd:marius@goodworkaround.com |
| UserName | no flow |
| AccountName | no flow – SharePoint will automatically populate this with something like “i:0\.t|SAML Users|marius@goodworkaround.com“ |
Windows authentication
To configure Windows authentication the following attributes needs to be flowed from FIM to SharePoint:
| SharePoint attribute | Value |
| SPS-ClaimProviderID | Constant: “Windows” |
| SPS-ClaimProviderType | Constant: “Windows” |
| SID | ObjectSID from Active Directory |
| ProfileIdentifier | DOMAIN\sAMAccountName from Active Directory |
| UserName | sAMAccountName from Active Directory |
| AccountName | Do not flow anything |
Example user
| SharePoint attribute | Value |
| SPS-ClaimProviderID | Windows |
| SPS-ClaimProviderType | Windows |
| SID | – binary data – |
| ProfileIdentifier | GWRND\marius |
| UserName | marius |
| AccountName | no flow |
That’s, hope it saves you some time.