Quick blogpost about the experience of AAD authentication for Windows VMs – https://docs.microsoft.com/en-us/azure/active-directory/devices/howto-vm-sign-in-azure-ad-windows
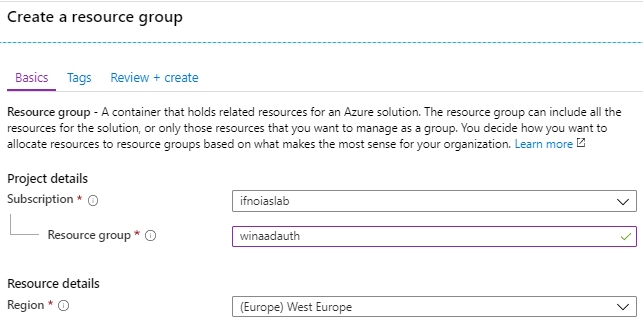
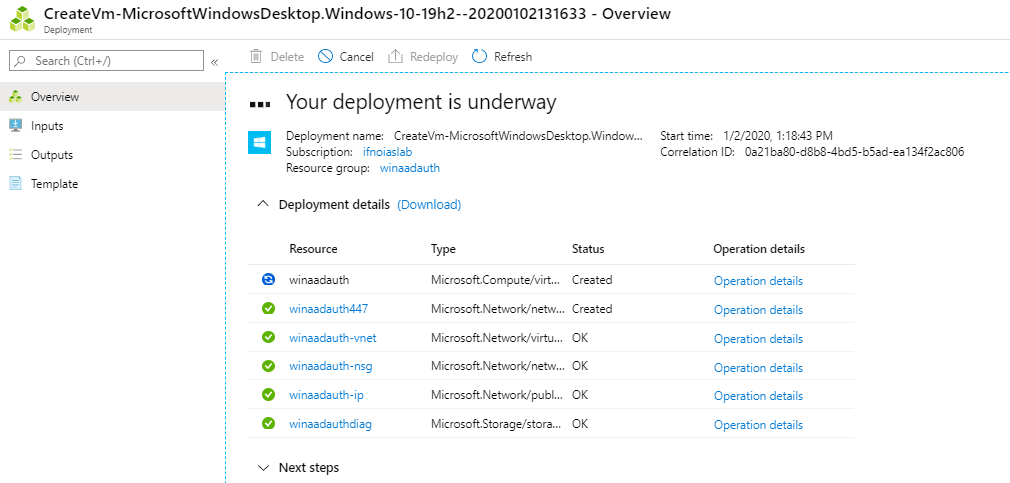
Creating a separate resource group for easy deletion…
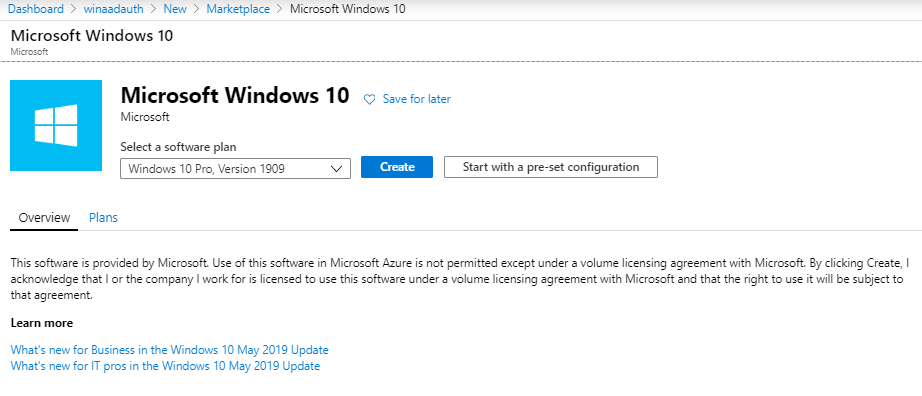
Let’s try out Windows 10 1909
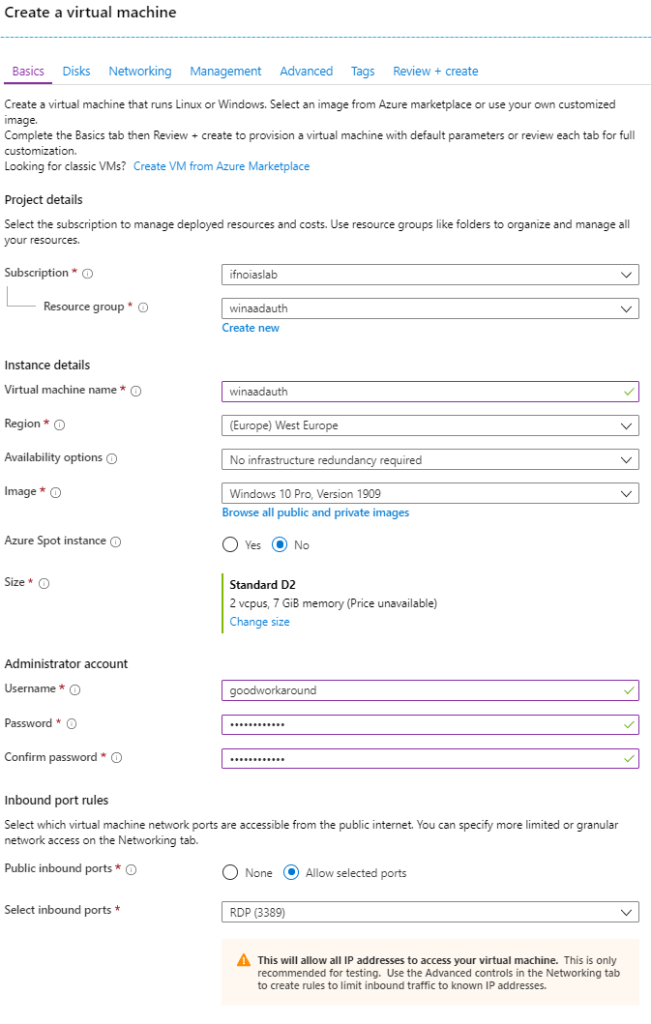
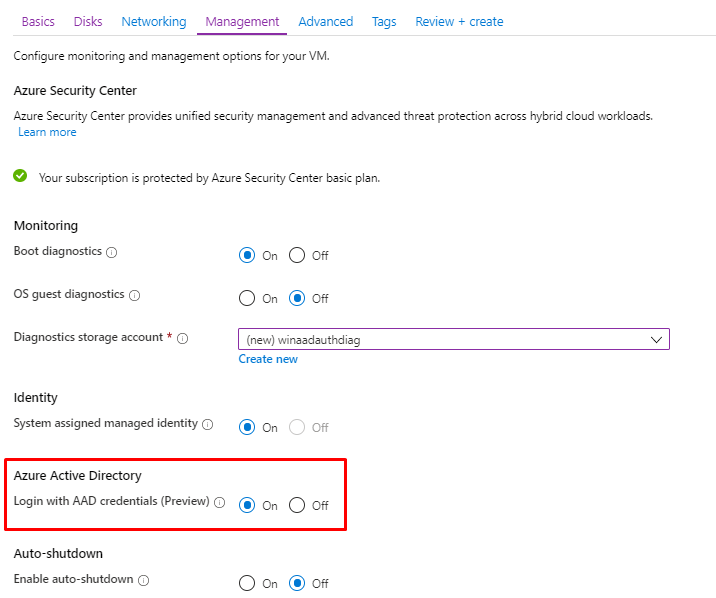
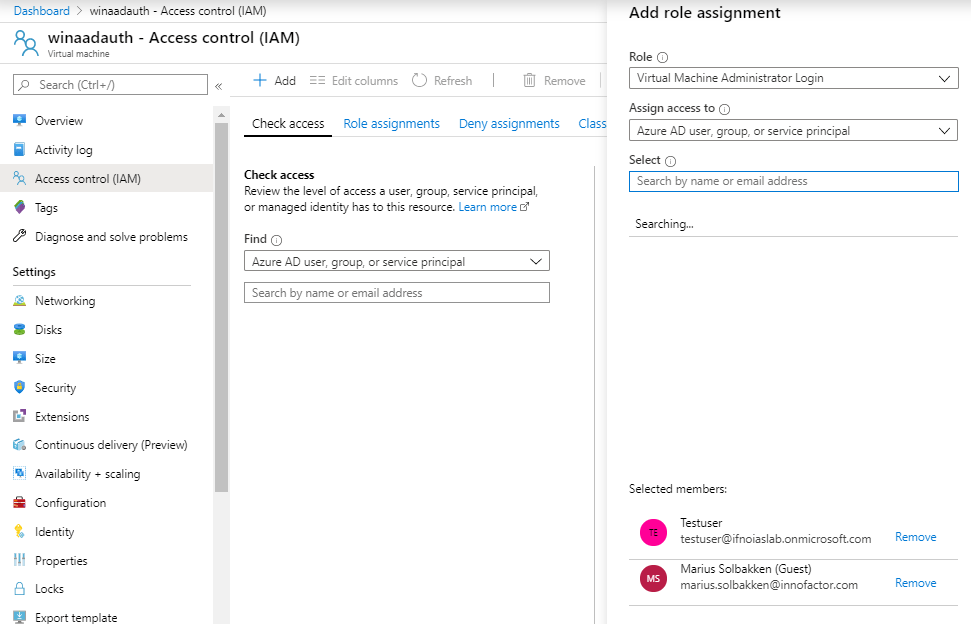
Following the documentation, we need to add role assignments in the Azure portal. Trying with both a local user and a guest account, though the documentation states that the VM must be connected to the same Azure AD as the user, meaning B2B account will not work.
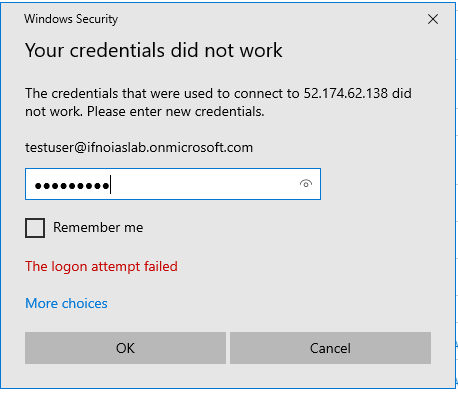
Well, that didn’t work:
An hey, reading through the documentation before actually trying it out, would have told me the following:
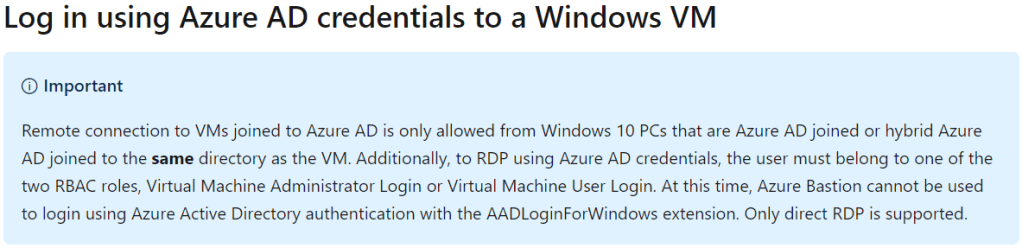
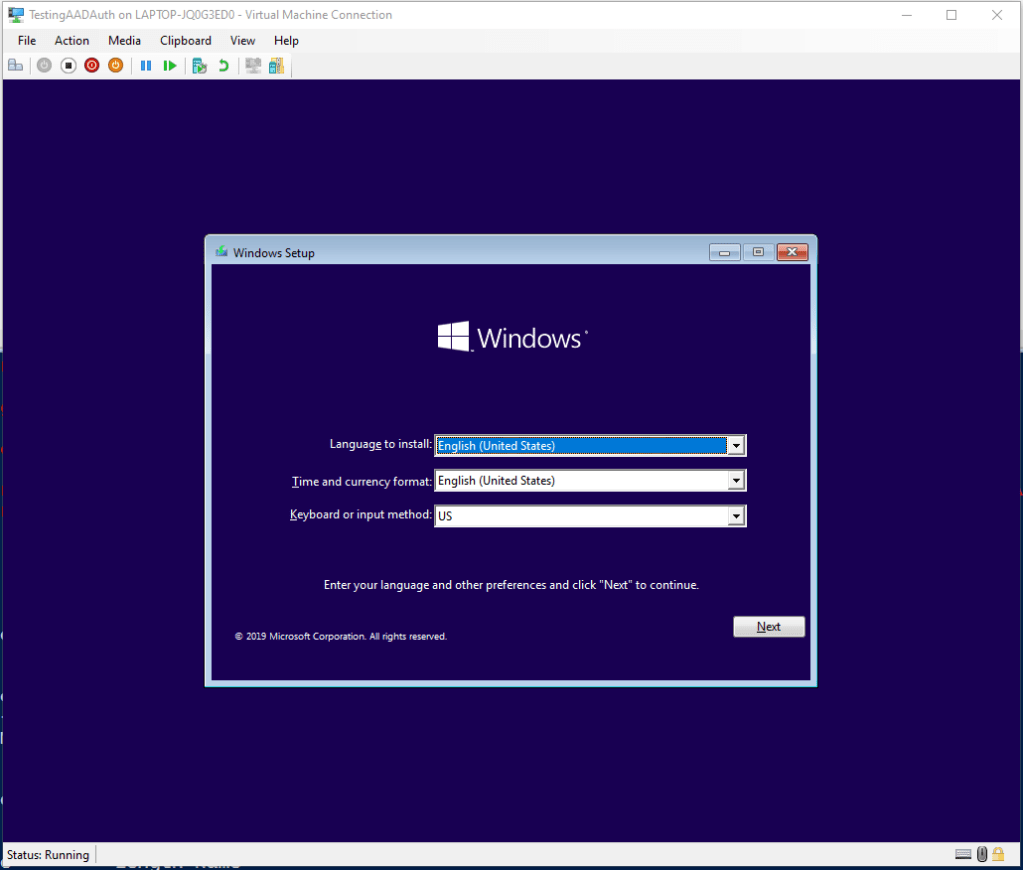
Well, that’s a bummer to be honest. Installing a Hyper-V VM for this purpose locally, as I want to have a fully Azure AD Joined device to test from:
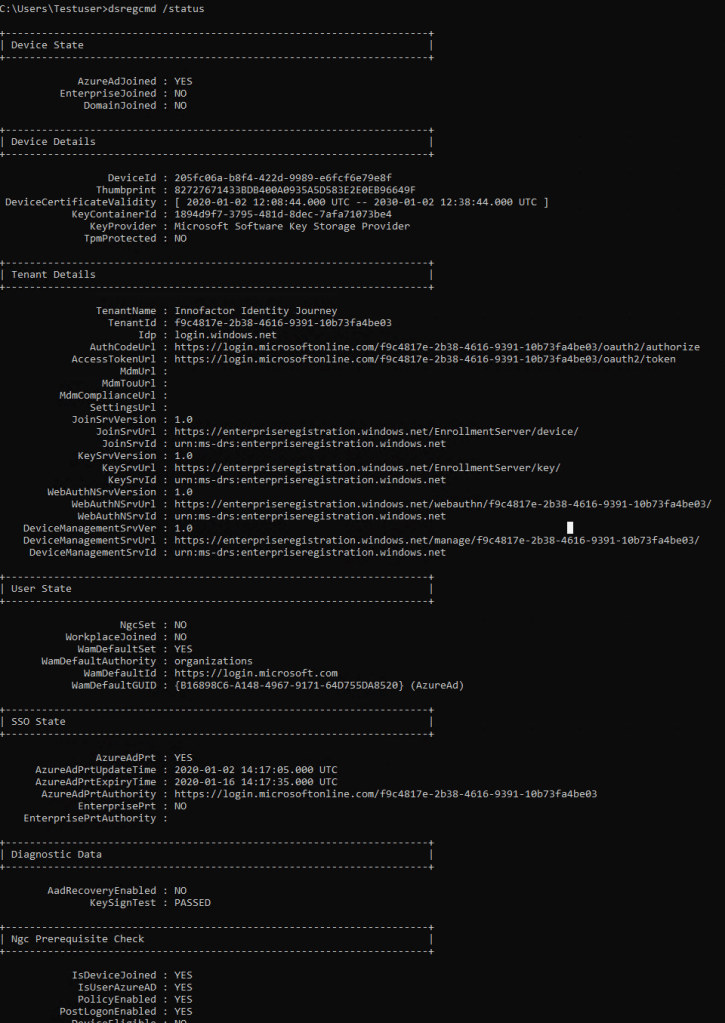
After Azure AD joining a VM successfully and running dsregcmd /status, we see that I now have a PRT for the correct tenant:

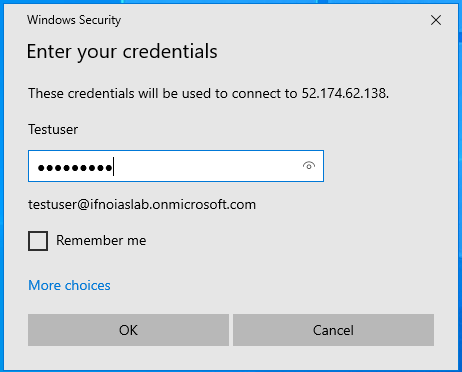
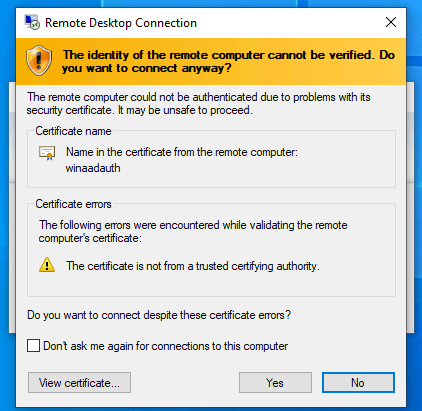
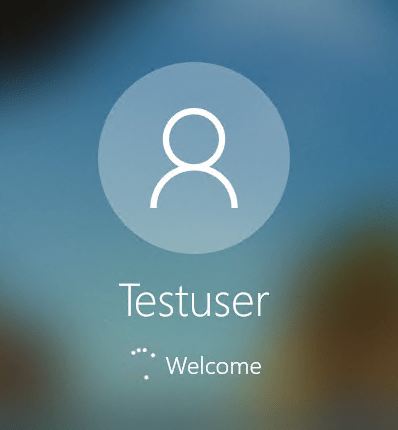
And voila, it worked just fine. The Windows 10 Azure VM login works!
I think the whole “you need to sign in from a computer joined to the same Azure AD” situation is a huge limitation, so let’s hope this is solved at some point.