The docs.microsoft.com pages contain several examples for managing Entitlement Management, however, you can never get enough examples. Also, an end to end example can be useful some times, so here you go.
This blog post assumes you have knowledge on how to get yourself an access token, and how to provide it as a bearer token in the authorization header.
All of the JSON examples can be tested using the Graph Explorer, where you will need the following permissions:
- Group.ReadWrite.All
- Application.ReadWrite.All
- EntitlementManagement.ReadWrite.All
Creating a single tenant application with application roles
An application is very straight forward to create, but requires a small trick for enabling it as an enterprise application. First, you need to create an application through the https://graph.microsoft.com/v1.0/applications endpoint:
POST https://graph.microsoft.com/v1.0/applications
{
"signInAudience": "AzureADMyOrg",
"displayName": "My blog post",
"appRoles": [
{
"displayName": "Administrator",
"value": "Administrator",
"allowedMemberTypes": [
"User"
],
"description": "Provides administrator access",
"id": "6cac1224-3c38-4268-9dce-3c0a1de3b967",
"isEnabled": true,
"origin": "Application"
},
{
"displayName": "User",
"value": "User",
"allowedMemberTypes": [
"User"
],
"description": "Provides user access",
"id": "d87d0026-6343-4ec5-b05b-4cd3ced5e61b",
"isEnabled": true,
"origin": "Application"
}
]
}
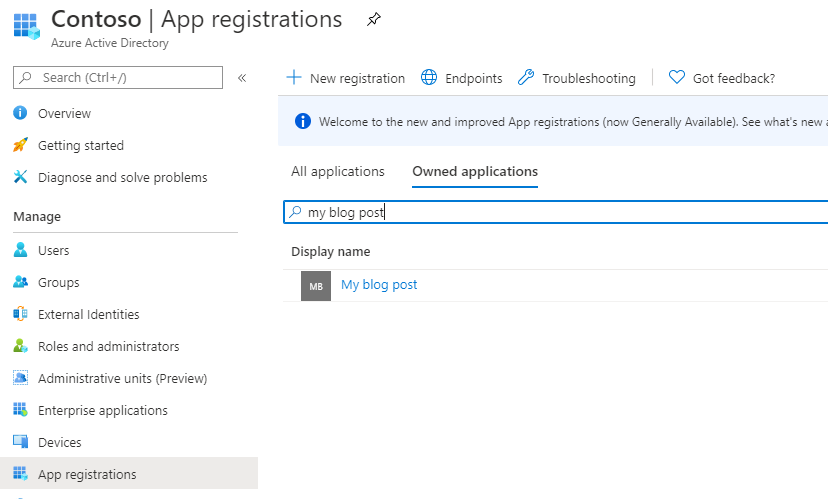
If you look in the Azure Portal at this point, you will find this application under “App registration”, but not under Enterprise Applications:

The reason for this, is that there is no servicePrincipal connected to this app registration. In order to create a servicePrincipal, we will need to use the client id of the app registration, returned as “appid” from the Graph. The POST will contain this value, which in my case was ‘2f45b02e-1a4b-4838-8cdf-864f7442e517’:

In order to create the servicePrincipal, a POST to https://graph.microsoft.com/beta/servicePrincipals must happen, with the appId. Also, note that I add a tag, which is important. If the tag WindowsAzureActiveDirectoryIntegratedApp is not there, the enterprise application will still not be displayed.
POST https://graph.microsoft.com/v1.0/servicePrincipals
{
"tags": [
"WindowsAzureActiveDirectoryIntegratedApp"
],
"appId": "2f45b02e-1a4b-4838-8cdf-864f7442e517"
}
At this point the enterprise application will show up, and you can assign users to the defined roles:


Creating an Entitlement Management catalog
Creating a catalog is very straight forward, and requires one of the following permissions:
- Global Administrator
- User Administrator
- Catalog Creator (Not an Azure AD role)
POST https://graph.microsoft.com/beta/identityGovernance/entitlementManagement/accessPackageCatalogs
{
"description": "Contains access package for blog post",
"isExternallyVisible": false,
"displayName": "My blog post catalog"
}
The catalog has been created. Please note the “id” returned, which is the object id of the catalog, as this is what we need to use when linking resources to the catalog, or creating access packages:

Adding an application as a resource to a catalog
For adding an application as a resource to a catalog, I did a lot digging around, eventually looking at the API calls the Azure Portal makes, in order to understand how to do this.
If you are not a global administrator, but only a catalog creator, you as of June 3rd will get a very strange error message (some ADAL internal stuff, even though you are not using ADAL), so make sure you are a global administrator when trying this.
In order to register an application as a resource, an “access package resource request” must be sent as follows, with originId being the objectid of the service principal of the enterprise application (!) (which is the object id of your enterprise application):

POST https://graph.microsoft.com/beta/identityGovernance/entitlementManagement/accessPackageResourceRequests
{
"catalogId": "dc0c7837-2578-433c-a799-488681305355",
"requestType": "AdminAdd",
"justification": "",
"accessPackageResource": {
"description": null,
"originId": "a866310d-b230-4fef-a23a-165f2e97f1e4",
"displayName": "My blog post",
"originSystem": "AadApplication"
}
}
If all goes well, you should receive something like the following response:
{
"@odata.context": "https://graph.microsoft.com/beta/$metadata#accessPackageResourceRequests/$entity",
"catalogId": "dc0c7837-2578-433c-a799-488681305355",
"executeImmediately": false,
"id": "b50866d0-dd44-4d31-9aef-9e66ea5c8e46",
"requestType": "AdminAdd",
"requestState": "Delivered",
"requestStatus": "Fulfilled",
"isValidationOnly": false,
"expirationDateTime": null,
"justification": ""
}
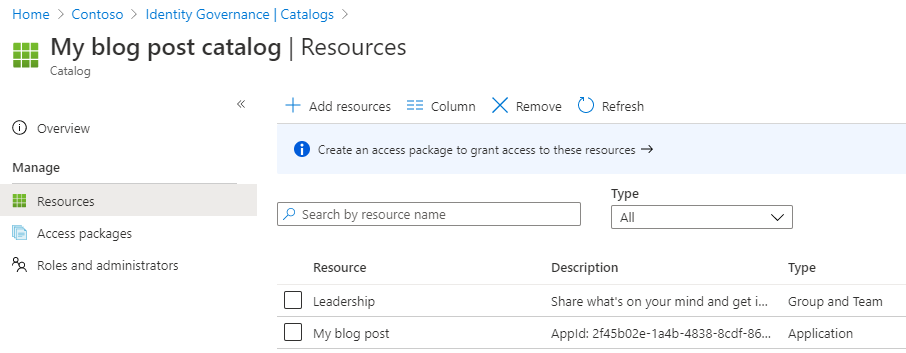
We will now find our application listed under “Resources”, in our catalog:

Please note: The displayName you provide will be visible to users, and cannot currently be changed. If you change the name of the application, the displayName of the resource remains the same as before. I have reported this issue to Microsoft.
Adding a group as a resource to a catalog
Adding a group is just as simple as adding an application. The difference is that the originSystem must be AadGroup and the originId must be the object id of the group we want to add:

POST https://graph.microsoft.com/beta/identityGovernance/entitlementManagement/accessPackageResourceRequests
{
"catalogId": "dc0c7837-2578-433c-a799-488681305355",
"requestType": "AdminAdd",
"justification": "",
"accessPackageResource": {
"description": null,
"originId": "bfa61c08-6a44-41cb-9f21-bac442d238ff",
"displayName": "Leadership",
"originSystem": "AadGroup"
}
}
This is our response:
{
"@odata.context": "https://graph.microsoft.com/beta/$metadata#accessPackageResourceRequests/$entity",
"catalogId": "dc0c7837-2578-433c-a799-488681305355",
"executeImmediately": false,
"id": "d45a785c-560f-4675-9c6f-532031f424d6",
"requestType": "AdminAdd",
"requestState": "Delivered",
"requestStatus": "Fulfilled",
"isValidationOnly": false,
"expirationDateTime": null,
"justification": ""
}
Please note: The displayName you provide will be visible to users, and cannot currently be changed. If you change the name of the group, the displayName of the resource remains the same as before. I have reported this issue to Microsoft.
Creating an access package with a policy and linked resources
Creating an access package is actually at least three POST operations, potentially more if you are linking multiple resources and adding several policies.
Creating the access package
First, let’s start by creating the access package in itself. This is essentially the object that we will add policies and resources to.
POST https://graph.microsoft.com/beta/identityGovernance/entitlementManagement/accessPackages
{
"catalogId": "dc0c7837-2578-433c-a799-488681305355",
"displayName": "Blog demo",
"description": "Some description required",
"isHidden": false
}
Now, again, you will need to note the “id” returned, which is the object id of the access package. We will need this for our next calls:

Assigning “member of a group” to an access package
Now we are really down the rabit hole… I am sure there are reasons for this API being so complex, but it makes things difficult to understand.
First of all, you will need to GET something first, which is the catalog resources’ roles, called accessPackageResourceRoles, but in order to get THOSE, we first need to know the ID of the resource….
So first we need to get either ALL the accessPackageResource for the catalog, and find the group we wat to add:
GET https://graph.microsoft.com/beta/identityGovernance/entitlementManagement/accessPackageCatalogs/dc0c7837-2578-433c-a799-488681305355/accessPackageResourcesOr we can filter on the group we want by filtering on originId:
GET https://graph.microsoft.com/beta/identityGovernance/entitlementManagement/accessPackageCatalogs/dc0c7837-2578-433c-a799-488681305355/accessPackageResources?$filter=originId eq 'bfa61c08-6a44-41cb-9f21-bac442d238ff'Notice that the dc0c7837-2578-433c-a799-488681305355 value is our catalog’s object id and bfa61c08-6a44-41cb-9f21-bac442d238ff is our group’s object id.
Through this result, we will find the accessPackageResource object for our group:
{
"@odata.context": "https://graph.microsoft.com/beta/$metadata#accessPackageResources",
"value": [
{
"id": "83467ea2-b4d0-4d4a-9ca6-a892e24030a8",
"displayName": "Leadership",
"description": "Share what's on your mind and get important announcements from Patti and the rest of the Leadership Team.",
"url": "https://account.activedirectory.windowsazure.com/r?tenantId=e955400e-9d6e-4a45-8698-cda2d2eeba4b#/manageMembership?objectType=Group&objectId=bfa61c08-6a44-41cb-9f21-bac442d238ff",
"resourceType": "O365 Group",
"originId": "bfa61c08-6a44-41cb-9f21-bac442d238ff",
"originSystem": "AadGroup",
"isPendingOnboarding": false,
"addedBy": "admin@M365x720355.onmicrosoft.com",
"addedOn": "2020-06-03T21:37:12.267Z"
}
]
}
Going from here, we can use the “id” of our accessPackageResource to find the resource roles available. This is the same as you see here i the GUI:

GET https://graph.microsoft.com/beta/identityGovernance/entitlementManagement/accessPackageCatalogs/dc0c7837-2578-433c-a799-488681305355/accessPackageResourceRoles?$filter=(originSystem+eq+%27AadGroup%27+and+accessPackageResource/id+eq+%2783467ea2-b4d0-4d4a-9ca6-a892e24030a8%27)&$expand=accessPackageResourceThis will return something like the following for an “assigned” / “manual member” Office 365 group:
{
"@odata.context": "https://graph.microsoft.com/beta/$metadata#identityGovernance/entitlementManagement/accessPackageCatalogs('dc0c7837-2578-433c-a799-488681305355')/accessPackageResourceRoles(accessPackageResource())",
"value": [
{
"id": "00000000-0000-0000-0000-000000000000",
"displayName": "Owner",
"description": null,
"originSystem": "AadGroup",
"originId": "Owner_bfa61c08-6a44-41cb-9f21-bac442d238ff",
"accessPackageResource@odata.context": "https://graph.microsoft.com/beta/$metadata#identityGovernance/entitlementManagement/accessPackageCatalogs('dc0c7837-2578-433c-a799-488681305355')/accessPackageResourceRoles('00000000-0000-0000-0000-000000000000')/accessPackageResource/$entity",
"accessPackageResource": {
"id": "83467ea2-b4d0-4d4a-9ca6-a892e24030a8",
"displayName": "Leadership",
"description": "Share what's on your mind and get important announcements from Patti and the rest of the Leadership Team.",
"url": "https://account.activedirectory.windowsazure.com/r?tenantId=e955400e-9d6e-4a45-8698-cda2d2eeba4b#/manageMembership?objectType=Group&objectId=bfa61c08-6a44-41cb-9f21-bac442d238ff",
"resourceType": "O365 Group",
"originId": "bfa61c08-6a44-41cb-9f21-bac442d238ff",
"originSystem": "AadGroup",
"isPendingOnboarding": false,
"addedBy": "admin@M365x720355.onmicrosoft.com",
"addedOn": "2020-06-03T21:37:12.267Z"
}
},
{
"id": "00000000-0000-0000-0000-000000000000",
"displayName": "Member",
"description": null,
"originSystem": "AadGroup",
"originId": "Member_bfa61c08-6a44-41cb-9f21-bac442d238ff",
"accessPackageResource@odata.context": "https://graph.microsoft.com/beta/$metadata#identityGovernance/entitlementManagement/accessPackageCatalogs('dc0c7837-2578-433c-a799-488681305355')/accessPackageResourceRoles('00000000-0000-0000-0000-000000000000')/accessPackageResource/$entity",
"accessPackageResource": {
"id": "83467ea2-b4d0-4d4a-9ca6-a892e24030a8",
"displayName": "Leadership",
"description": "Share what's on your mind and get important announcements from Patti and the rest of the Leadership Team.",
"url": "https://account.activedirectory.windowsazure.com/r?tenantId=e955400e-9d6e-4a45-8698-cda2d2eeba4b#/manageMembership?objectType=Group&objectId=bfa61c08-6a44-41cb-9f21-bac442d238ff",
"resourceType": "O365 Group",
"originId": "bfa61c08-6a44-41cb-9f21-bac442d238ff",
"originSystem": "AadGroup",
"isPendingOnboarding": false,
"addedBy": "admin@M365x720355.onmicrosoft.com",
"addedOn": "2020-06-03T21:37:12.267Z"
}
}
]
}
If you add a dynamic group as a resource in a catalog, you will actually only see “Owner” being available, which is quite nifty 🙂
In order to link “Member of group” as a resource role to our access package, an accessPackageResourceRoleScope object must be created. This object essentially contains an accessPackageResourceScope, which is our group resource, and an accessPackageResourceRole, which is one of the roles we just got.
POST https://graph.microsoft.com/beta/identityGovernance/entitlementManagement/accessPackages/c17bcf57-bac2-492e-9b6e-90aaa9c59686/accessPackageResourceRoleScopes
{
"accessPackageResourceRole": {
"id": "00000000-0000-0000-0000-000000000000",
"displayName": "Member",
"description": null,
"originSystem": "AadGroup",
"originId": "Member_bfa61c08-6a44-41cb-9f21-bac442d238ff",
"accessPackageResource": {
"id": "83467ea2-b4d0-4d4a-9ca6-a892e24030a8",
"displayName": "Leadership",
"description": "Share what's on your mind and get important announcements from Patti and the rest of the Leadership Team.",
"url": "https://account.activedirectory.windowsazure.com/r?tenantId=e955400e-9d6e-4a45-8698-cda2d2eeba4b#/manageMembership?objectType=Group&objectId=bfa61c08-6a44-41cb-9f21-bac442d238ff",
"resourceType": "O365 Group",
"originId": "bfa61c08-6a44-41cb-9f21-bac442d238ff",
"originSystem": "AadGroup",
"isPendingOnboarding": false,
"addedBy": "admin@M365x720355.onmicrosoft.com",
"addedOn": "2020-06-03T21:37:12.267Z"
}
},
"accessPackageResourceScope": {
"originId": "bfa61c08-6a44-41cb-9f21-bac442d238ff",
"originSystem": "AadGroup"
}
}
If you look closely, the accessPackageResourceRole is an exact copy of the object returned from the accessPackageResourceRoles endpoint, with only the accessPackageResource@odata.context attribute removed.
Actually, if we really want to limit the amount of required attributes in our POST we can do like this:
POST https://graph.microsoft.com/beta/identityGovernance/entitlementManagement/accessPackages/c17bcf57-bac2-492e-9b6e-90aaa9c59686/accessPackageResourceRoleScopes
{
"accessPackageResourceRole": {
"originSystem": "AadGroup",
"originId": "Member_bfa61c08-6a44-41cb-9f21-bac442d238ff",
"accessPackageResource": {
"id": "83467ea2-b4d0-4d4a-9ca6-a892e24030a8",
"originSystem": "AadGroup"
}
},
"accessPackageResourceScope": {
"originId": "bfa61c08-6a44-41cb-9f21-bac442d238ff",
"originSystem": "AadGroup"
}
}
The end result will be the following group being added to our access package:

Assigning an application with a role to an access package
Assigning an application with a certain role is actually almost the same as assigning a group in the previous section, so I will keep it more simple.
First get the accessPackageResource of the application using the following GET, where dc0c7837-2578-433c-a799-488681305355 is the object id of your catalog, and a866310d-b230-4fef-a23a-165f2e97f1e4 being the object id of your enterprise application:
GET https://graph.microsoft.com/beta/identityGovernance/entitlementManagement/accessPackageCatalogs/dc0c7837-2578-433c-a799-488681305355/accessPackageResources?$filter=originId eq 'a866310d-b230-4fef-a23a-165f2e97f1e4'The following application resource is returned for me:
{
"@odata.context": "https://graph.microsoft.com/beta/$metadata#accessPackageResources",
"value": [
{
"id": "fd2a37dc-4cf0-45b7-8dbe-f8672c3880d2",
"displayName": "My blog post",
"description": "AppId: 2f45b02e-1a4b-4838-8cdf-864f7442e517",
"url": "https://myapps.microsoft.com/M365x720355.onmicrosoft.com/signin/My%20blog%20post/2f45b02e-1a4b-4838-8cdf-864f7442e517/",
"resourceType": "Application",
"originId": "a866310d-b230-4fef-a23a-165f2e97f1e4",
"originSystem": "AadApplication",
"isPendingOnboarding": false,
"addedBy": "admin@M365x720355.onmicrosoft.com",
"addedOn": "2020-06-03T21:08:16.9Z"
}
]
}
Now I have the ID fd2a37dc-4cf0-45b7-8dbe-f8672c3880d2, that I can use to query the accessPackageResourceRoles endpoint for the relevant roles:
GET https://graph.microsoft.com/beta/identityGovernance/entitlementManagement/accessPackageCatalogs/dc0c7837-2578-433c-a799-488681305355/accessPackageResourceRoles?$filter=(originSystem+eq+%27AadApplication%27+and+accessPackageResource/id+eq+%27fd2a37dc-4cf0-45b7-8dbe-f8672c3880d2%27)&$expand=accessPackageResourceHere I will find my two application roles returned:
{
"@odata.context": "https://graph.microsoft.com/beta/$metadata#identityGovernance/entitlementManagement/accessPackageCatalogs('dc0c7837-2578-433c-a799-488681305355')/accessPackageResourceRoles(accessPackageResource())",
"value": [
{
"id": "00000000-0000-0000-0000-000000000000",
"displayName": "User",
"description": "Provides user access",
"originSystem": "AadApplication",
"originId": "d87d0026-6343-4ec5-b05b-4cd3ced5e61b",
"accessPackageResource@odata.context": "https://graph.microsoft.com/beta/$metadata#identityGovernance/entitlementManagement/accessPackageCatalogs('dc0c7837-2578-433c-a799-488681305355')/accessPackageResourceRoles('00000000-0000-0000-0000-000000000000')/accessPackageResource/$entity",
"accessPackageResource": {
"id": "fd2a37dc-4cf0-45b7-8dbe-f8672c3880d2",
"displayName": "My blog post",
"description": "AppId: 2f45b02e-1a4b-4838-8cdf-864f7442e517",
"url": "https://myapps.microsoft.com/M365x720355.onmicrosoft.com/signin/My%20blog%20post/2f45b02e-1a4b-4838-8cdf-864f7442e517/",
"resourceType": "Application",
"originId": "a866310d-b230-4fef-a23a-165f2e97f1e4",
"originSystem": "AadApplication",
"isPendingOnboarding": false,
"addedBy": "admin@M365x720355.onmicrosoft.com",
"addedOn": "2020-06-03T21:08:16.9Z"
}
},
{
"id": "00000000-0000-0000-0000-000000000000",
"displayName": "Administrator",
"description": "Provides administrator access",
"originSystem": "AadApplication",
"originId": "6cac1224-3c38-4268-9dce-3c0a1de3b967",
"accessPackageResource@odata.context": "https://graph.microsoft.com/beta/$metadata#identityGovernance/entitlementManagement/accessPackageCatalogs('dc0c7837-2578-433c-a799-488681305355')/accessPackageResourceRoles('00000000-0000-0000-0000-000000000000')/accessPackageResource/$entity",
"accessPackageResource": {
"id": "fd2a37dc-4cf0-45b7-8dbe-f8672c3880d2",
"displayName": "My blog post",
"description": "AppId: 2f45b02e-1a4b-4838-8cdf-864f7442e517",
"url": "https://myapps.microsoft.com/M365x720355.onmicrosoft.com/signin/My%20blog%20post/2f45b02e-1a4b-4838-8cdf-864f7442e517/",
"resourceType": "Application",
"originId": "a866310d-b230-4fef-a23a-165f2e97f1e4",
"originSystem": "AadApplication",
"isPendingOnboarding": false,
"addedBy": "admin@M365x720355.onmicrosoft.com",
"addedOn": "2020-06-03T21:08:16.9Z"
}
}
]
}
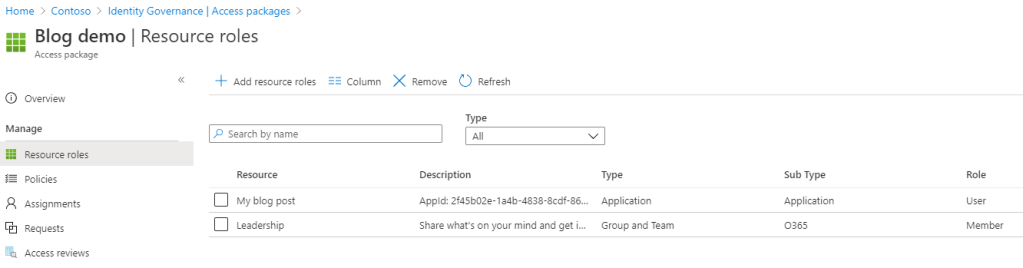
This of course matches my roles available in the GUI:

Now, using the simplified version from the assigning group section, we can POST the following:
POST https://graph.microsoft.com/beta/identityGovernance/entitlementManagement/accessPackages/c17bcf57-bac2-492e-9b6e-90aaa9c59686/accessPackageResourceRoleScopes
{
"accessPackageResourceRole": {
"originSystem": "AadApplication",
"originId": "d87d0026-6343-4ec5-b05b-4cd3ced5e61b",
"accessPackageResource": {
"id": "fd2a37dc-4cf0-45b7-8dbe-f8672c3880d2",
"originSystem": "AadApplication"
}
},
"accessPackageResourceScope": {
"originId": "a866310d-b230-4fef-a23a-165f2e97f1e4",
"originSystem": "AadApplication"
}
}
And voila, our access package has the “User” role of our application added:
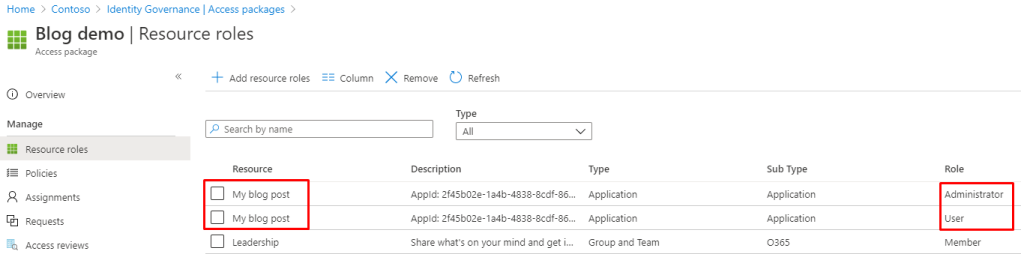
We can of course also add another role for the same application:
POST https://graph.microsoft.com/beta/identityGovernance/entitlementManagement/accessPackages/c17bcf57-bac2-492e-9b6e-90aaa9c59686/accessPackageResourceRoleScopes
{
"accessPackageResourceRole": {
"originSystem": "AadApplication",
"originId": "6cac1224-3c38-4268-9dce-3c0a1de3b967",
"accessPackageResource": {
"id": "fd2a37dc-4cf0-45b7-8dbe-f8672c3880d2",
"originSystem": "AadApplication"
}
},
"accessPackageResourceScope": {
"originId": "a866310d-b230-4fef-a23a-165f2e97f1e4",
"originSystem": "AadApplication"
}
}
Adding allow all external users policy to an access package
First, adjust the “Enabled for external users” setting to Yes:

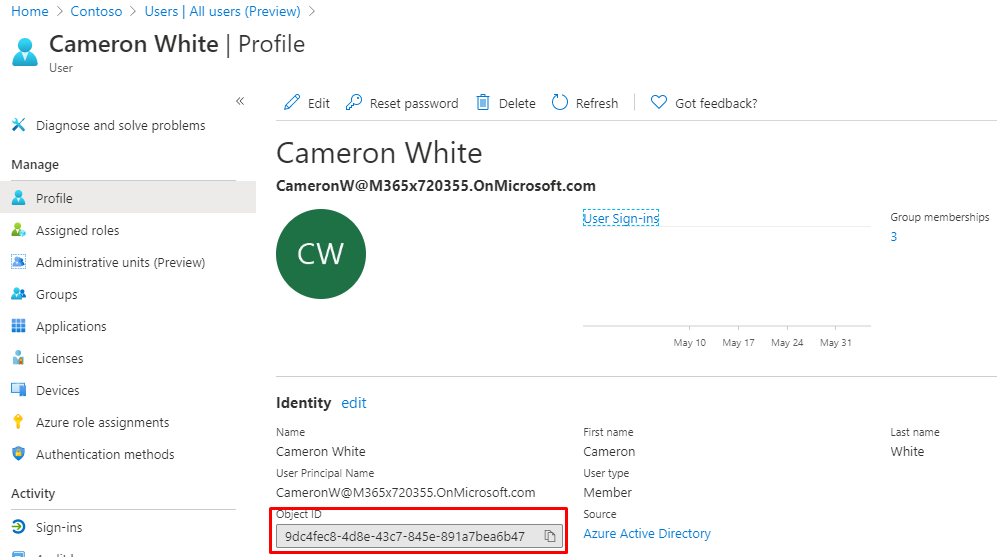
Then, locate either a group or a user that will be the approver of the requests, noting down the object id:
Now we are ready to add the policy:
POST https://graph.microsoft.com/beta/identityGovernance/entitlementManagement/accessPackageAssignmentPolicies
{
"requestApprovalSettings": {
"approvalMode": "SingleStage",
"approvalStages": [
{
"escalationTimeInMinutes": 0,
"primaryApprovers": [
{
"@odata.type": "#microsoft.graph.singleUser",
"id": "9dc4fec8-4d8e-43c7-845e-891a7bea6b47",
"isBackup": false,
"description": "Cameron White"
}
],
"approvalStageTimeOutInDays": 14,
"isEscalationEnabled": false,
"escalationApprovers": [],
"isApproverJustificationRequired": true
}
],
"isRequestorJustificationRequired": true,
"isApprovalRequiredForExtension": true,
"isApprovalRequired": true
},
"displayName": "Policy allowing anyone to request package",
"description": "Anyone can request this package, no B2B guest account required - but they must know the url",
"requestorSettings": {
"scopeType": "AllExternalSubjects",
"acceptRequests": true,
"allowedRequestors": []
},
"canExtend": true,
"durationInDays": 365,
"accessReviewSettings": null,
"accessPackageId": "c17bcf57-bac2-492e-9b6e-90aaa9c59686"
}
And voila:

Ok, so what the hell? How are you supposed to know you need to post all THAT stuff. Well, actually this is very easy. My recommended approach is – create it once in the GUI, get the policy you created through Graph and try to understand the parameters! Example:
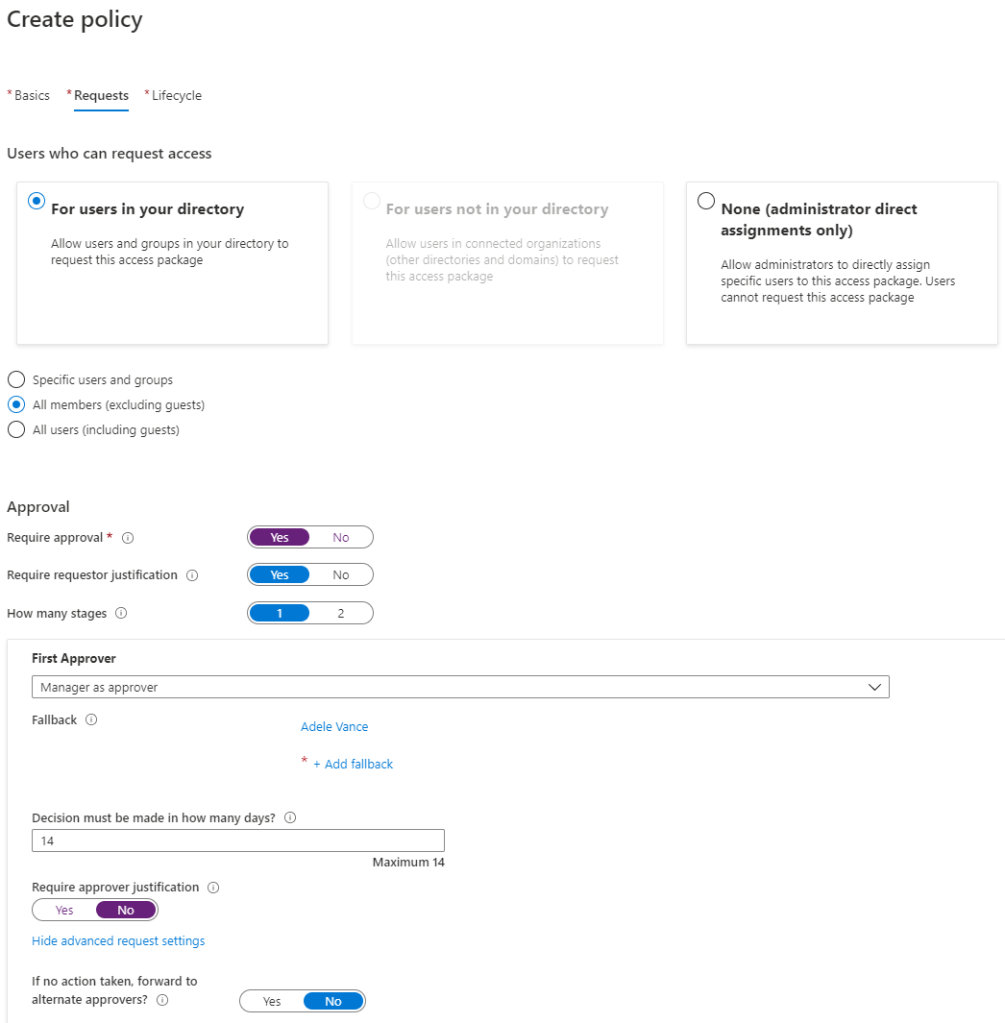
I create a policy which is a easy as it can be, with manager approval:


Now that we have our policy live, let’s GET it through Graph:
First locate the policy id:
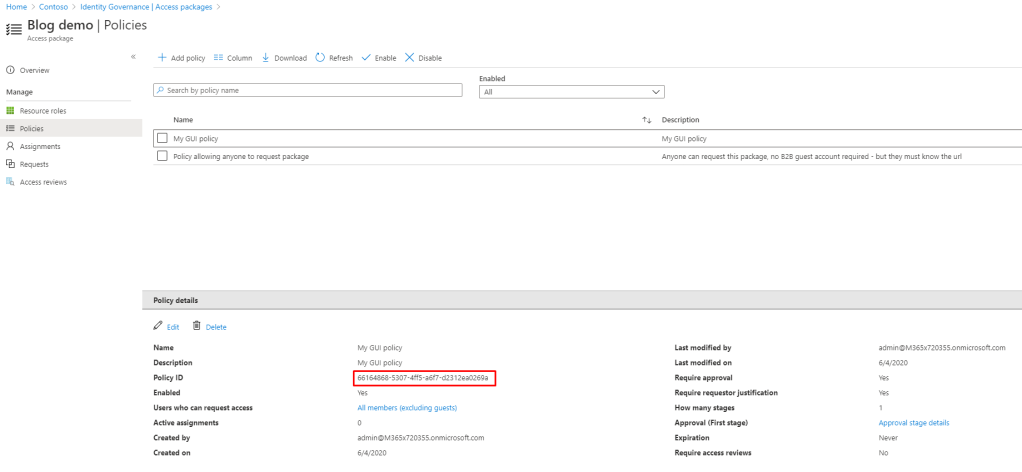
Second, GET it:
GET https://graph.microsoft.com/beta/identityGovernance/entitlementManagement/accessPackageAssignmentPolicies/66164868-5307-4ff5-a6f7-d2312ea0269aThis will return the following, that we can try to understand, posting it back with some changes:
{
"@odata.context": "https://graph.microsoft.com/beta/$metadata#accessPackageAssignmentPolicies/$entity",
"id": "66164868-5307-4ff5-a6f7-d2312ea0269a",
"accessPackageId": "c17bcf57-bac2-492e-9b6e-90aaa9c59686",
"displayName": "My GUI policy",
"description": "My GUI policy",
"canExtend": false,
"durationInDays": 0,
"expirationDateTime": null,
"createdBy": "admin@M365x720355.onmicrosoft.com",
"createdDateTime": "2020-06-03T23:02:11.55Z",
"modifiedBy": "admin@M365x720355.onmicrosoft.com",
"modifiedDateTime": "2020-06-03T23:02:12.363Z",
"accessReviewSettings": null,
"requestorSettings": {
"scopeType": "AllExistingDirectoryMemberUsers",
"acceptRequests": true,
"allowedRequestors": []
},
"requestApprovalSettings": {
"isApprovalRequired": true,
"isApprovalRequiredForExtension": false,
"isRequestorJustificationRequired": true,
"approvalMode": "SingleStage",
"approvalStages": [
{
"approvalStageTimeOutInDays": 14,
"isApproverJustificationRequired": false,
"isEscalationEnabled": false,
"escalationTimeInMinutes": 0,
"primaryApprovers": [
{
"@odata.type": "#microsoft.graph.singleUser",
"isBackup": true,
"id": "ffa5f048-e12a-4c10-98c7-2548a0f751a7",
"description": "Adele Vance"
},
{
"@odata.type": "#microsoft.graph.requestorManager",
"isBackup": false
}
],
"escalationApprovers": []
}
]
}
}
Here is a modified version that we are posting:
POST https://graph.microsoft.com/beta/identityGovernance/entitlementManagement/accessPackageAssignmentPolicies
{
"@odata.context": "https://graph.microsoft.com/beta/$metadata#accessPackageAssignmentPolicies/$entity",
"accessPackageId": "c17bcf57-bac2-492e-9b6e-90aaa9c59686",
"displayName": "My GUI policy (modified)",
"description": "My GUI policy (modified)",
"canExtend": false,
"durationInDays": 120,
"expirationDateTime": null,
"accessReviewSettings": null,
"requestorSettings": {
"scopeType": "AllExistingDirectoryMemberUsers",
"acceptRequests": true,
"allowedRequestors": []
},
"requestApprovalSettings": {
"isApprovalRequired": true,
"isApprovalRequiredForExtension": false,
"isRequestorJustificationRequired": true,
"approvalMode": "SingleStage",
"approvalStages": [
{
"approvalStageTimeOutInDays": 10,
"isApproverJustificationRequired": false,
"isEscalationEnabled": false,
"escalationTimeInMinutes": 0,
"primaryApprovers": [
{
"@odata.type": "#microsoft.graph.singleUser",
"isBackup": true,
"id": "467bd2e6-5603-4b31-958a-6d87b9f3aa85",
"description": "Joni Sherman"
},
{
"@odata.type": "#microsoft.graph.requestorManager",
"isBackup": false
}
],
"escalationApprovers": []
}
]
}
}
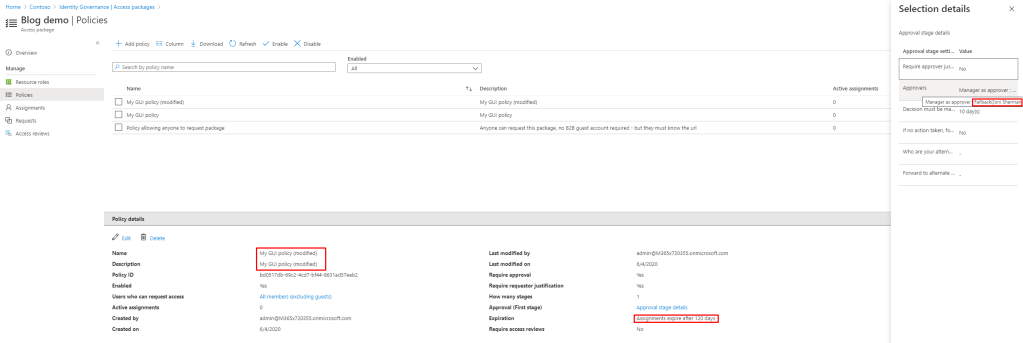
And here is my newly created policy, with some minor modifications:
That’s it. Hope these examples helps someone out. They sure will be a reference resource for me 🙂
Hello – In your post you mention “If you are not a global administrator, but only a catalog creator, you as of June 3rd will get a very strange error message ”
Where did you read this change?
I am experiencing the same issue, previously Global Admin was not required.
Just experienced it during a project 🙂
Hi Marius
Thank you very much for sharing this! It has saved me a lot of time messing around with the somewhat non-documented process of chaining the individual Graph calls.
There is one subject that you don’t touch, and for which I can find any Graph calls for either; Have you come across any means to programmatically add “Access package manager” and “Access package assignment manager” to a Catalog?
Two suggestions for you post:
* Add a reference in the top to your other post “”Birth right permissions using…”, as it describes to needed oauth with the delegated user. A troublesome discovery in itself…
* Perhaps make table or similar in this post around “In order to link “Member of group” as…” with the various id’s from the samples, I kind of got lost there a couple of times.
Regards,
/Per