The Azure REST API can be used to create most (or all?) types of resources in Azure, and can be useful when Terraform or ARM is too complex for your scenario or other reasons. I have now had the need to create KeyVaults from LogicApps, as a part of storing customer break glass account information. This is how I did it.
LogicApps has the ability to use Managed Service Identity, which greatly simplifies and increases security of our solution. Let’s go ahead and create a LogicApp, enabling Managed Service Identity, and prepare for working with the Azure API.
I assume you know how to simply create an empty LogicApp. Now go to “Identity” in the left menu, enable System Assigned identity and save. Next, click on the “Azure role assignments” button (the thing we are going to now can also be done through the ACLs on the resource group instead of this way).

Select your subscription and click “Add role assignment”.

Because we are creating stuff in a single resource group, we select the scope as “resource group”, select the resource group we want (marius-d-blogpost) and give the contributor role.

Now the LogicApp has all the access it needs. You can check under the “Access control (IAM)” menu on the resource group that the LogicApp has been granted its permissions:

Go to the LogicApp designer and add an HTTP trigger (or some other trigger you might need), and add an HTTP request as follows:

As this is a simple “let me show you how it works in its most simple way” type of blogpost, parameters and stuff will be hard coded. Let’s now first list all resources in our resource group as a step, again for demo purposes:

To get the authentication part, use the “add parameter” dropdown and click in the authentication checkbox.
For pastability, the url is here: https://management.azure.com/subscriptions/d74200b6-711c-4f24-9924-ab143a9644b6/resourceGroups/marius-d-blogpost/providers/Microsoft.KeyVault/vaults?api-version=2019-09-01
Let’s run the LogicApp and see what happens:
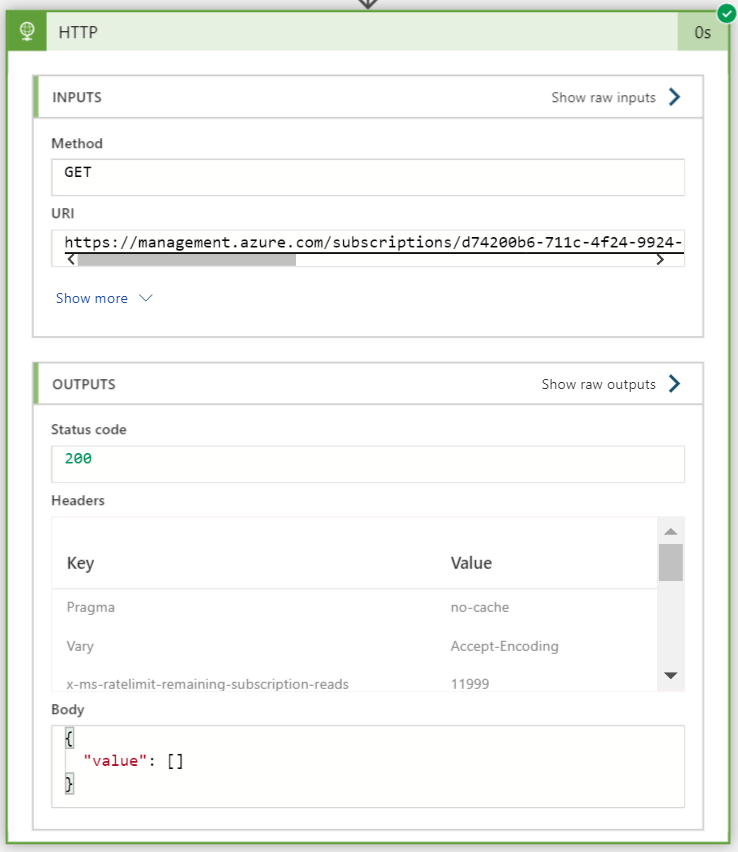
Voila (empty result, but that is correct), in just a few minutes we have already a LogicApp that can work with the Azure REST API. Now, let’s create a KeyVault ‘testvault’ using the PUT method as per the documentation:
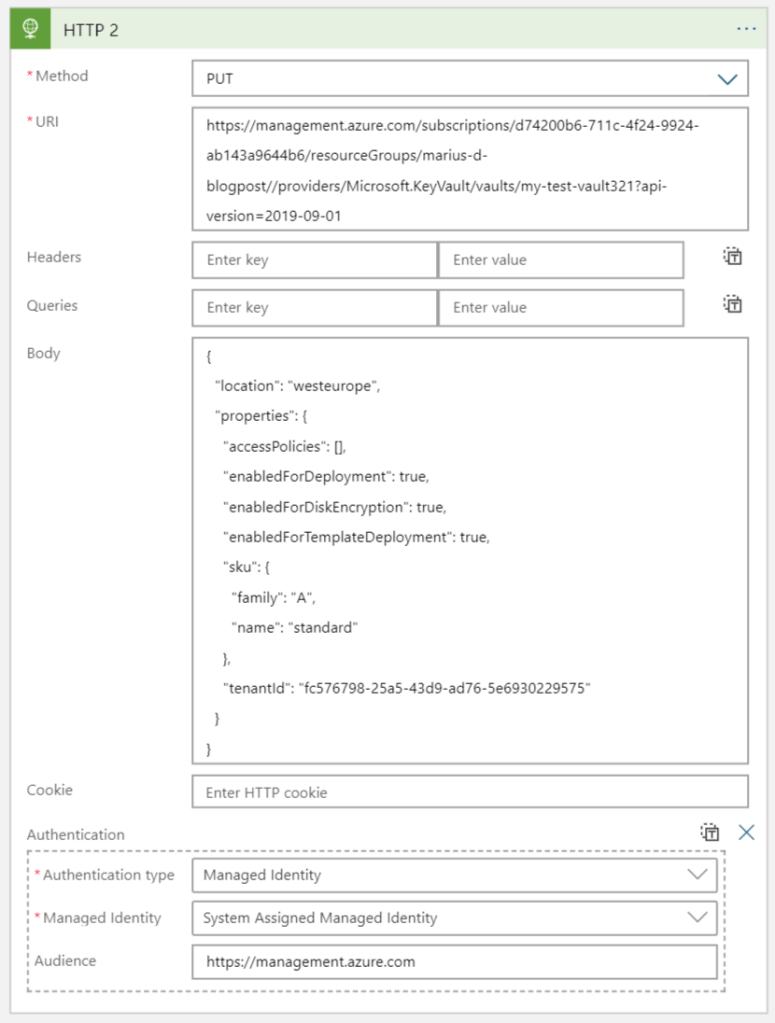
Again URL for pasting: https://management.azure.com/subscriptions/d74200b6-711c-4f24-9924-ab143a9644b6/resourceGroups/marius-d-blogpost/providers/Microsoft.KeyVault/vaults/my-test-vault321?api-version=2019-09-01
And here is the body:
{
"location": "westeurope",
"properties": {
"accessPolicies": [],
"enabledForDeployment": true,
"enabledForDiskEncryption": true,
"enabledForTemplateDeployment": true,
"sku": {
"family": "A",
"name": "standard"
},
"tenantId": "fc576798-25a5-43d9-ad76-5e6930229575"
}
}
Running the LogicApp now yields the following result:

That is it. I love how Managed Service Identities makes everything so darn easy!