The new option in Azure AD, allowing Azure AD Roles to be assigned to groups is very useful, and can be managed using Entitlement Management, for more extensive governance. No magic required.
Update: Just as an FYI, this feature will very soon be coming out of the box without the requirement of an Azure AD group “between” the access package and the Azure AD role.
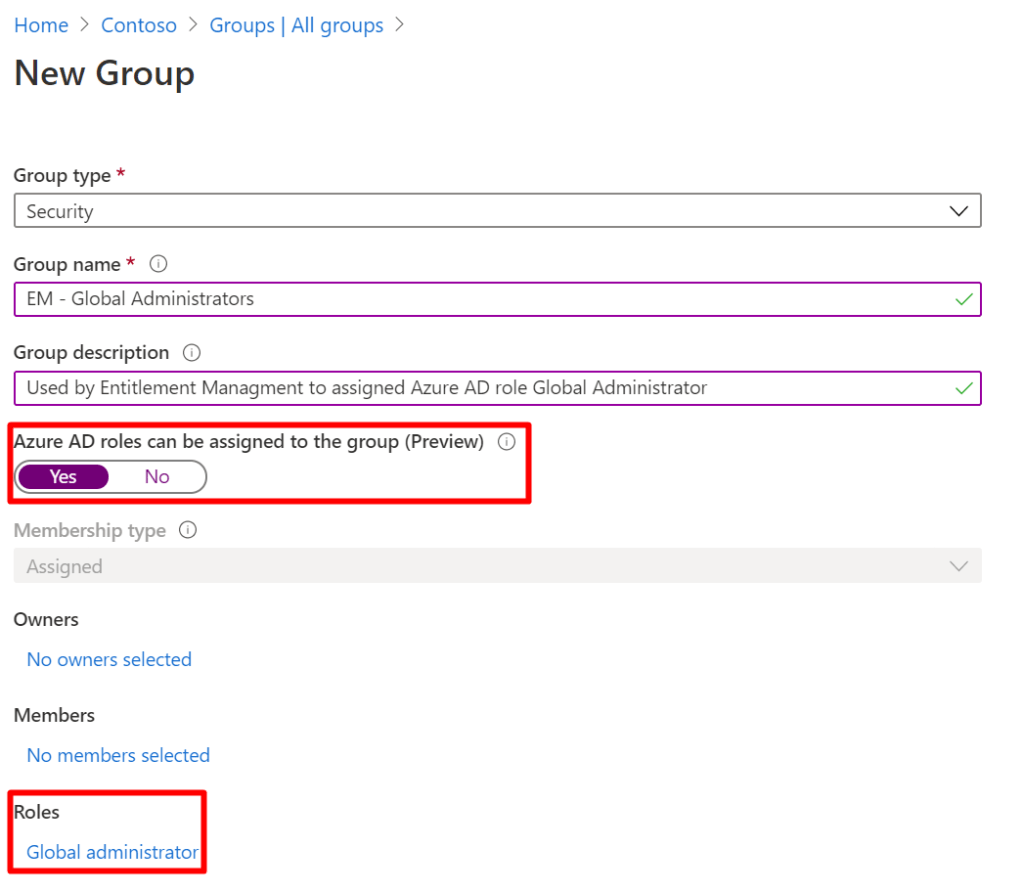
Start by creating a new Azure AD group, with the “Azure AD roles can be assigned ot the group” option enabled, and assigning the Global Administrator role.
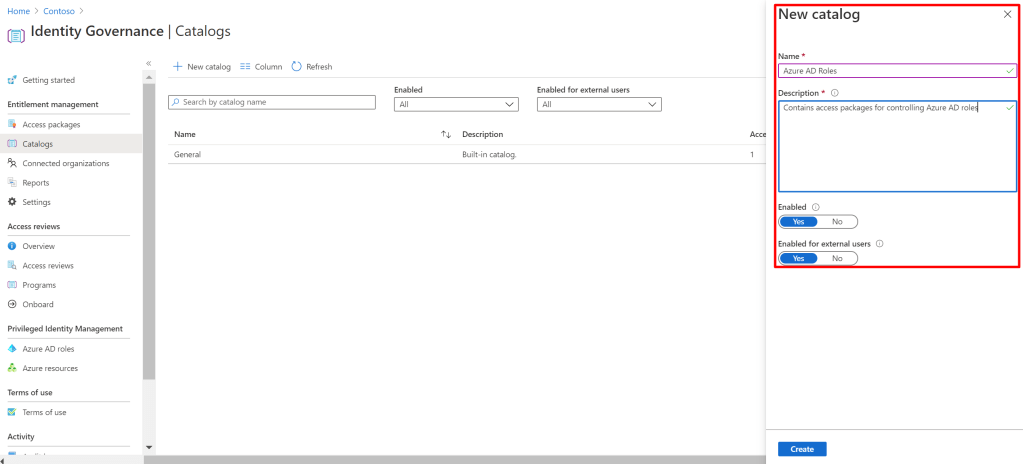
Next, go to Azure AD Entitlement Managment to create a new catalog. Since we are managing highly important roles, these access packages should be kept in a separate catalog.
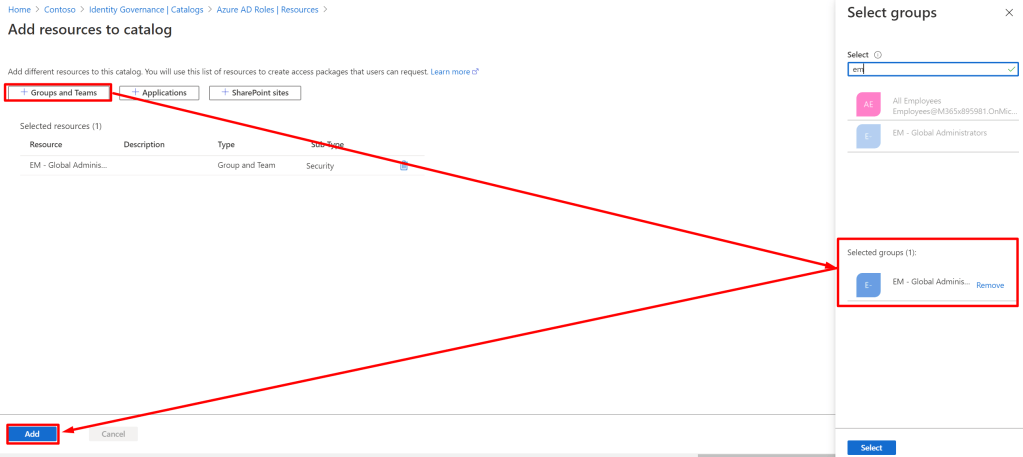
Next, go into the catalog, go to resource and “Add resources”:
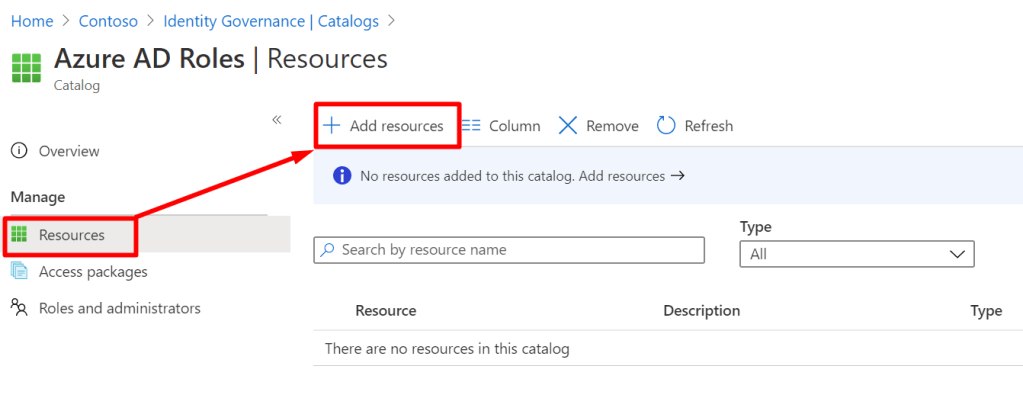
Now, add “Group or team”, find the group and click add:
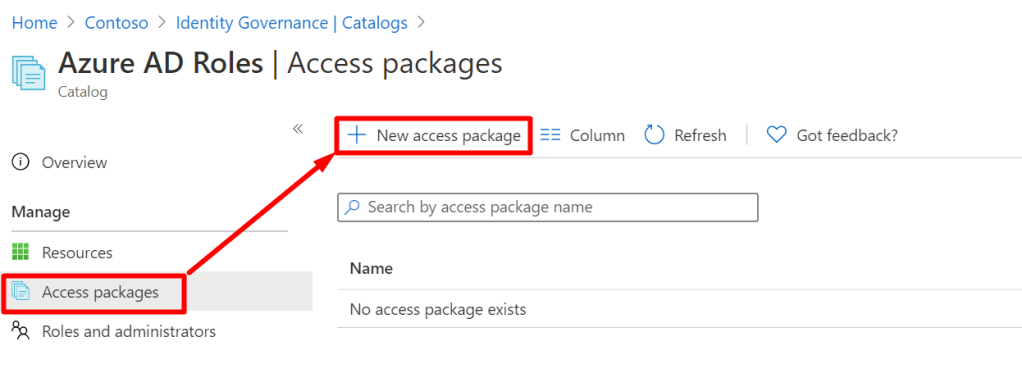
Now, go to “Access packages” and create a new access package:
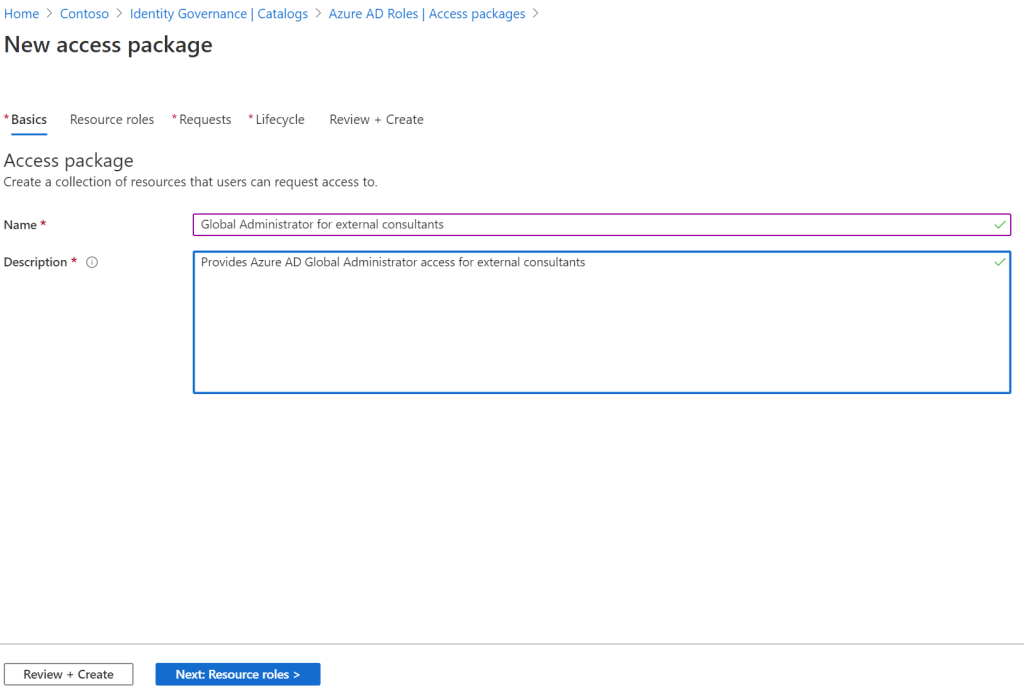
Give some kind of name and description to your access package (I am creating one for external users, granting Global Administrator):
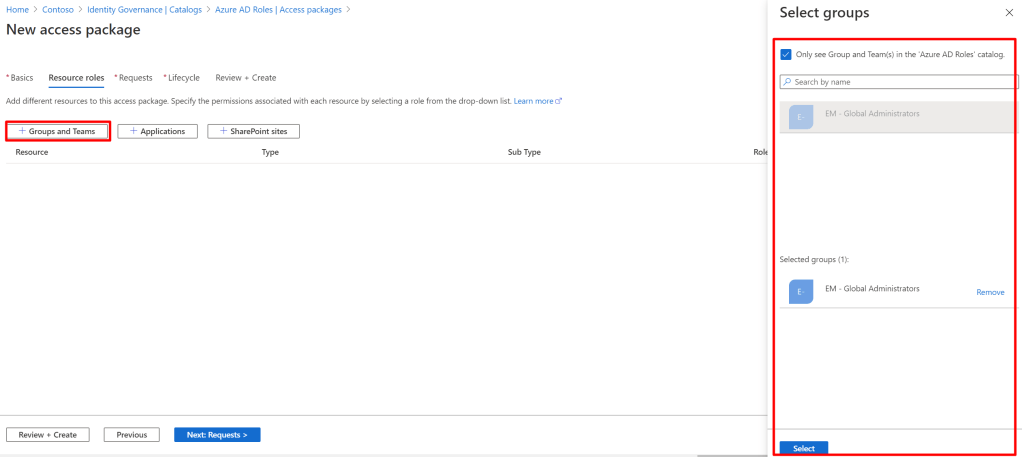
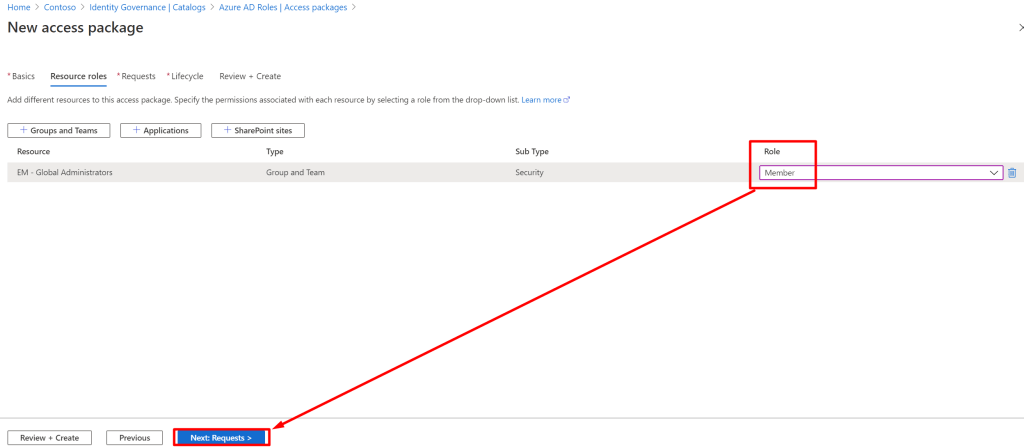
Link the group you added previously to your access package like this, and select “Member” as the role:
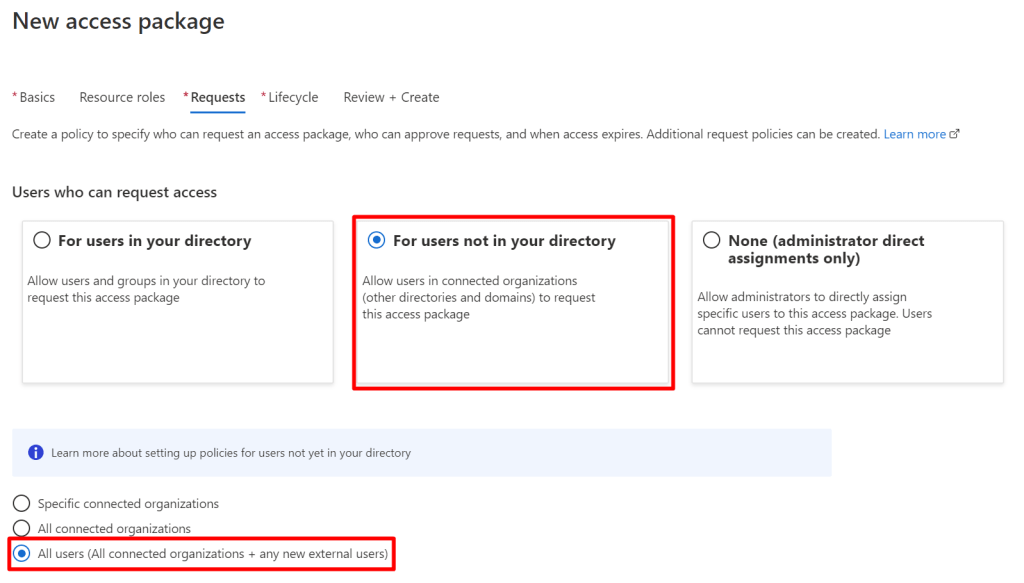
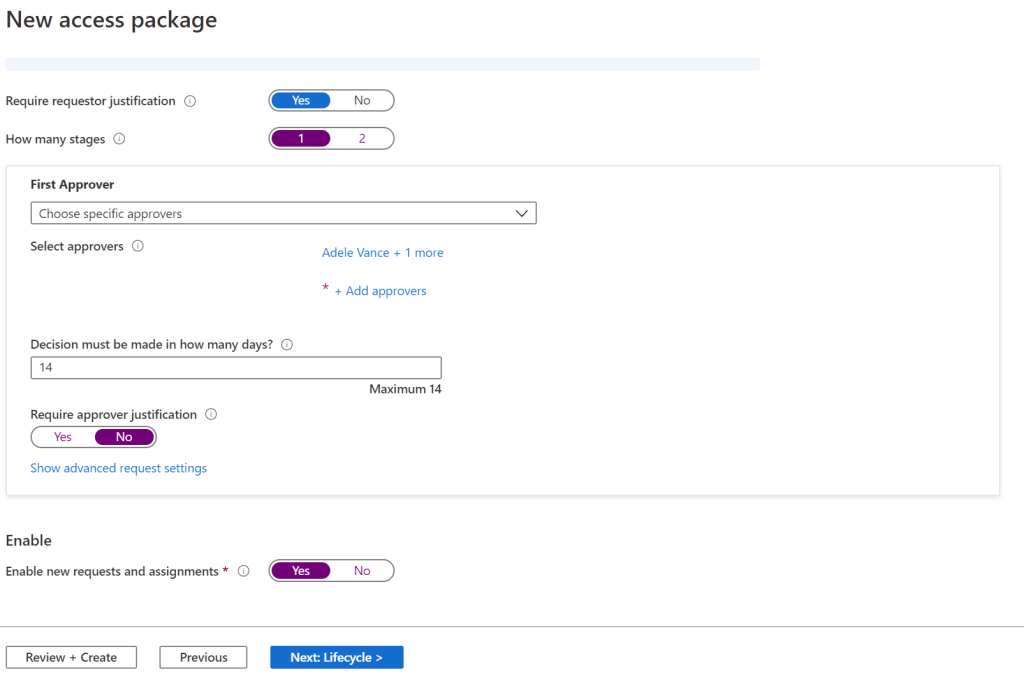
Next, we need to define our policy for who can request. I am creating an access package that anyone in the world can request (but I am going to make it hidden), with approval by a few people:
Now, since this is an important Azure AD role, I will set it to expire in 7 days:

After creating the access package, I’m hiding it to make sure that only people with the knowledge of the access package url will be able to request the access package:

Now I can test going to this url to request, with any external account.
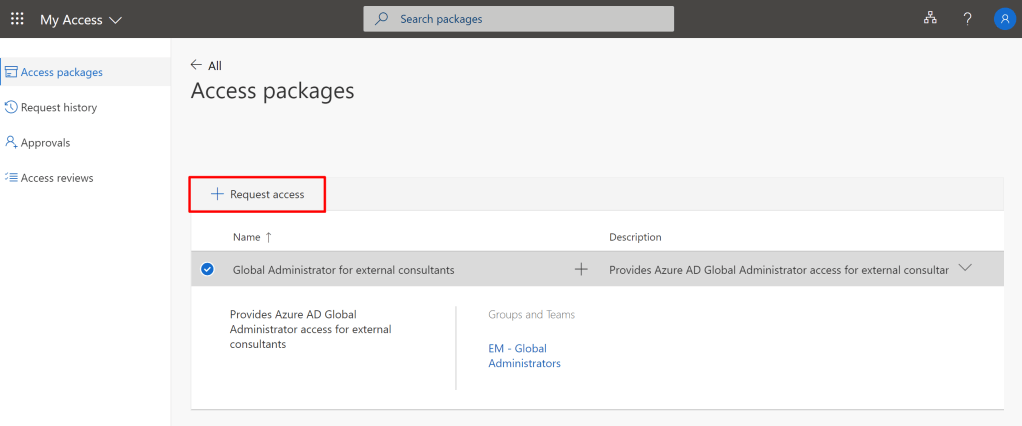
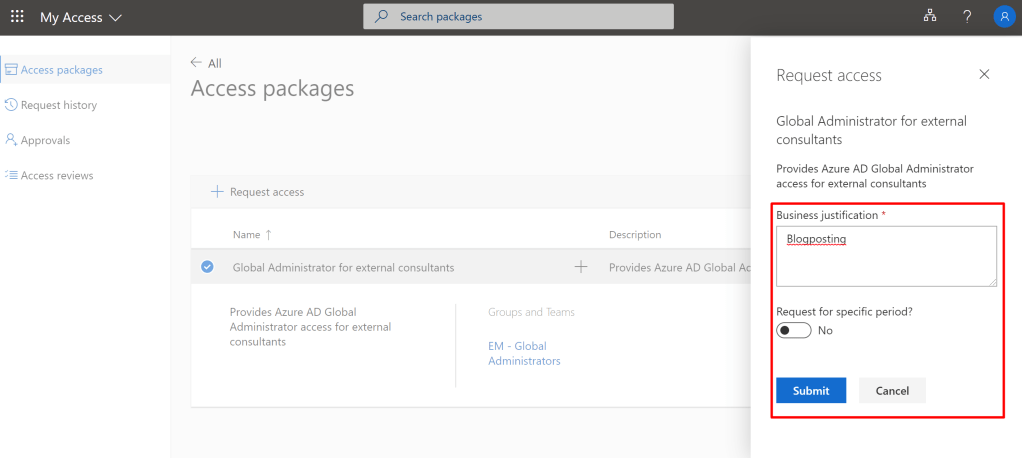
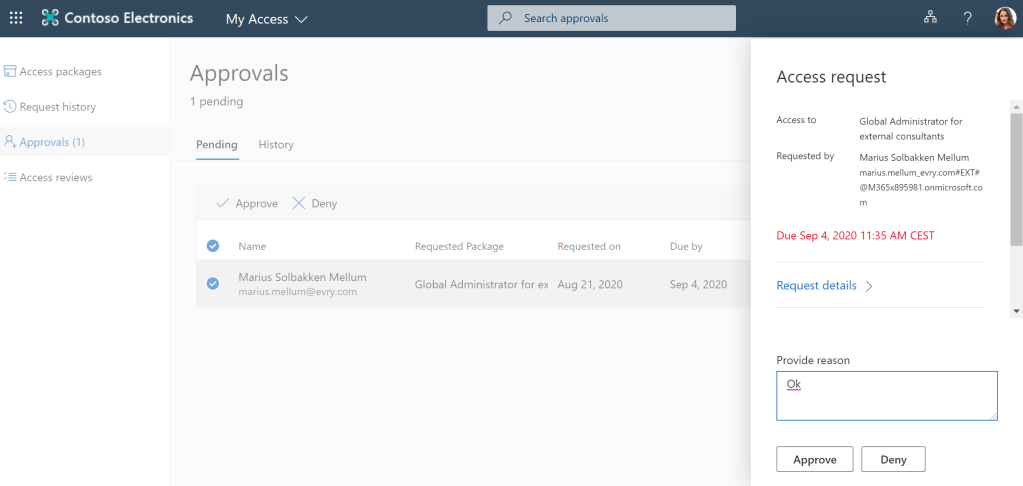
Adele, one of the approvers, can now approve the request in the myaccess portal:
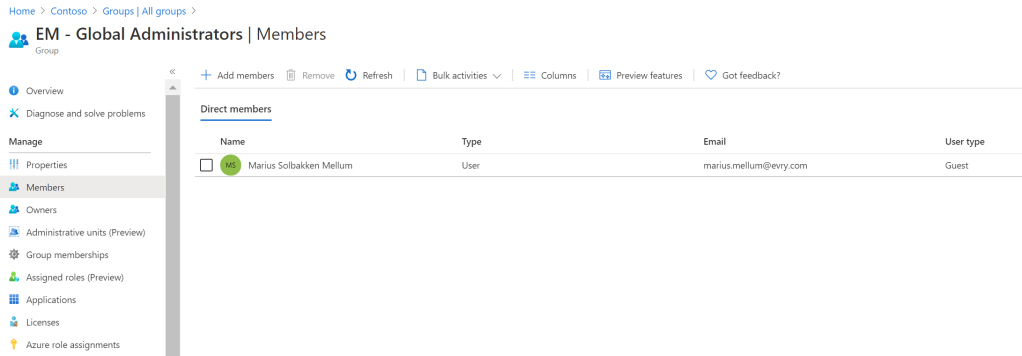
And voila, I am now a member of the “EM – Global Administrators” group, providing the Azure AD role:
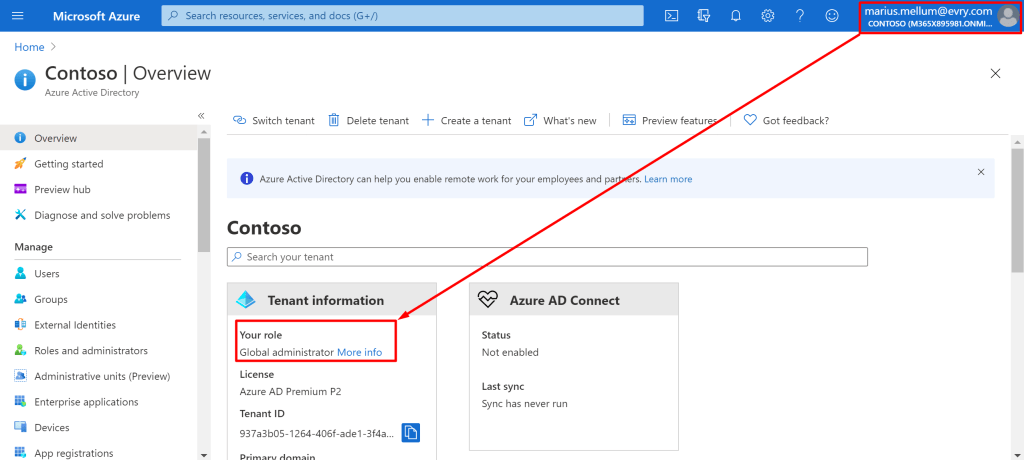
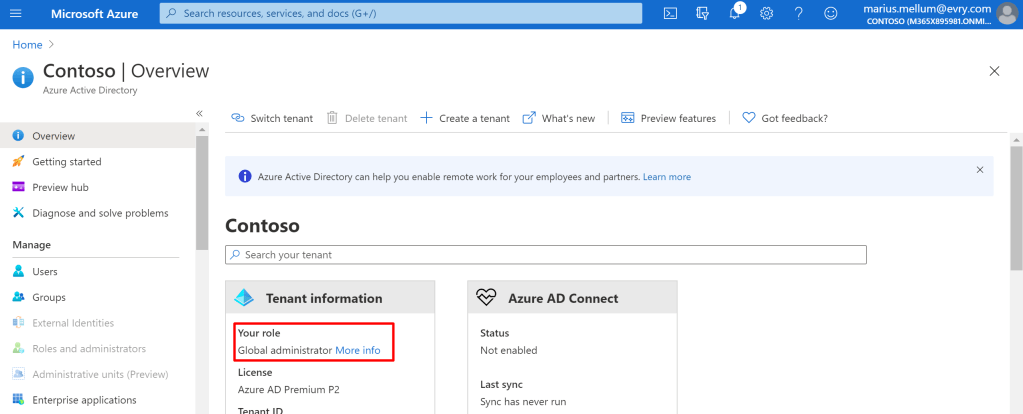
And, when accessing the Azure Portal using the account that requested access, it shows Global Administrator:
But what about PIM?
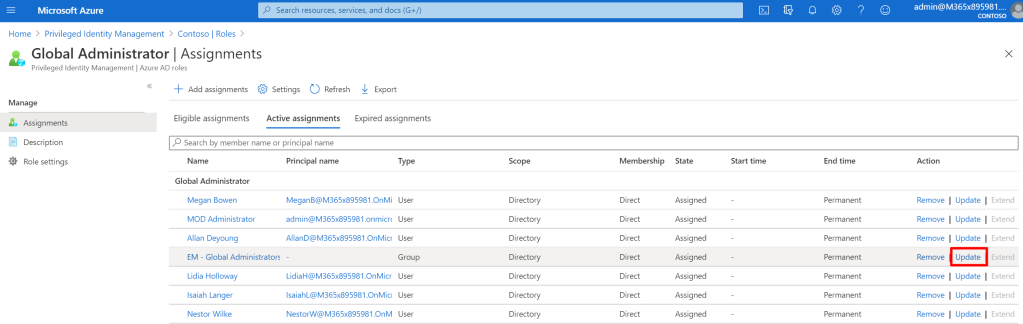
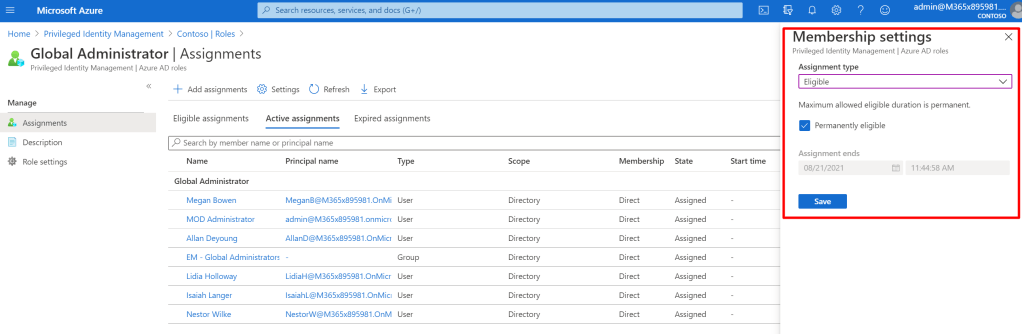
Actually, PIM is superb to combine with this! What we can do is to go to Azure AD PIM, and update the assignment for our group, converting it to an eligible assignment instead:
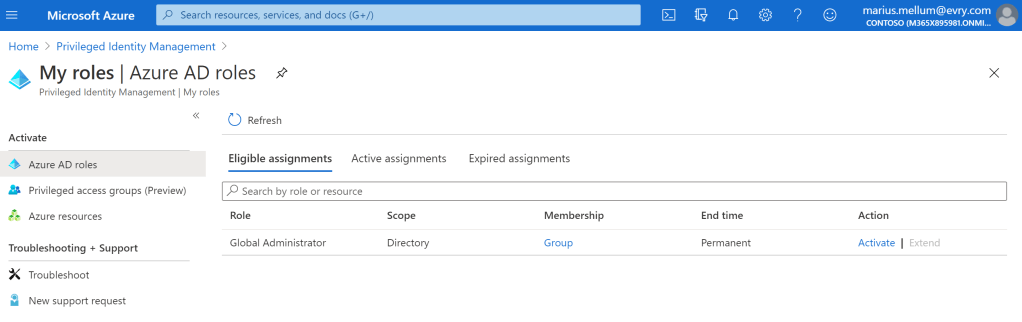
Now, the accounts that has requested the global administrator access package must also elevate to global admin using PIM!

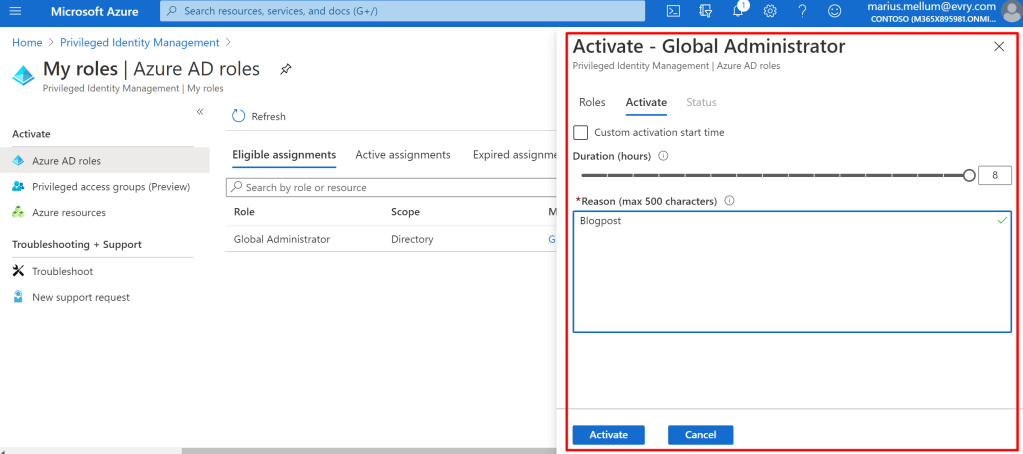

Voila, a better way of governing Azure AD Roles!